# Cyfinoid Research
> A research company focused on cyber security research
## Posts
### SBOMPlay v0.0.7
Date: 2025-12-31
URL: https://cyfinoid.com/sbomplay-v0-0-7/
> Put work out in the open, and the feedback turns into a roadmap.
SBOMPlay was presented at **[Black Hat EU Arsenal 2025](https://blackhat.com/eu-25/arsenal/schedule/index.html#sbom-play-48565)**.
The best part was not the stage time. It was the conversations that followed both during the demo and afterwards.
We got a steady stream of questions, edge cases, and “what if” scenarios from people who actually wanted to use the tool in their own workflows. That instantly expanded the idea pool and clarified what we should prioritize next.
So before we posted anything publicly about the Arsenal release, we took a short pause, put our heads down, and shipped the updates.
At the event, we demoed **[SBOMPlay v0.0.4](https://github.com/cyfinoid/sbomplay/releases/tag/v0.0.4)**.
Today, we are releasing **SBOMPlay v0.0.7**, an enhanced build with significantly more capability than what we showed at Arsenal.
In GitHub terms, the change set **[from v0.0.4 to v0.0.7](https://github.com/cyfinoid/sbomplay/compare/v0.0.4...v0.0.7)** was **61 files changed**, with **19,893 additions** and **8,992 deletions**.
## What is new in v0.0.7
Each of the updates below will be accompanied with a screenshot in the final post.
**Custom SBOM support**
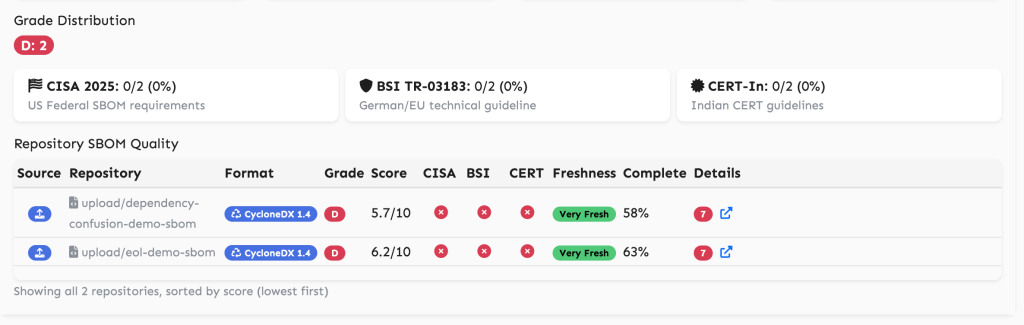
**Improved SBOM auditor** that checks against baselines like **CISA Minimum Elements** and **CERT-In**
**EOX detection** (EOL and EOS)
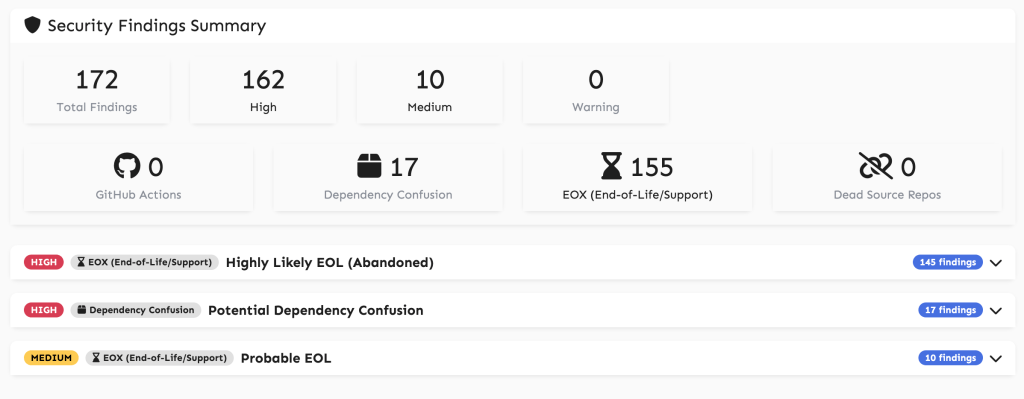
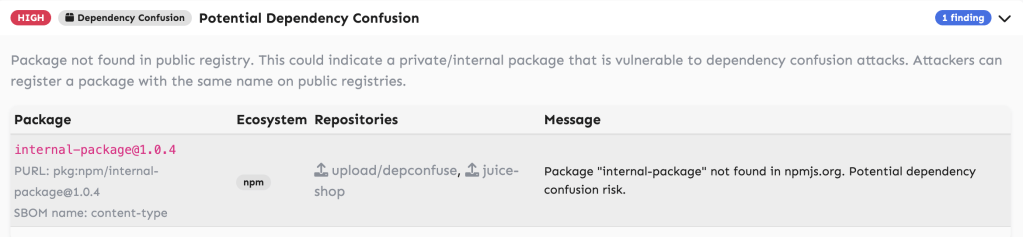
**Dependency confusion detection**
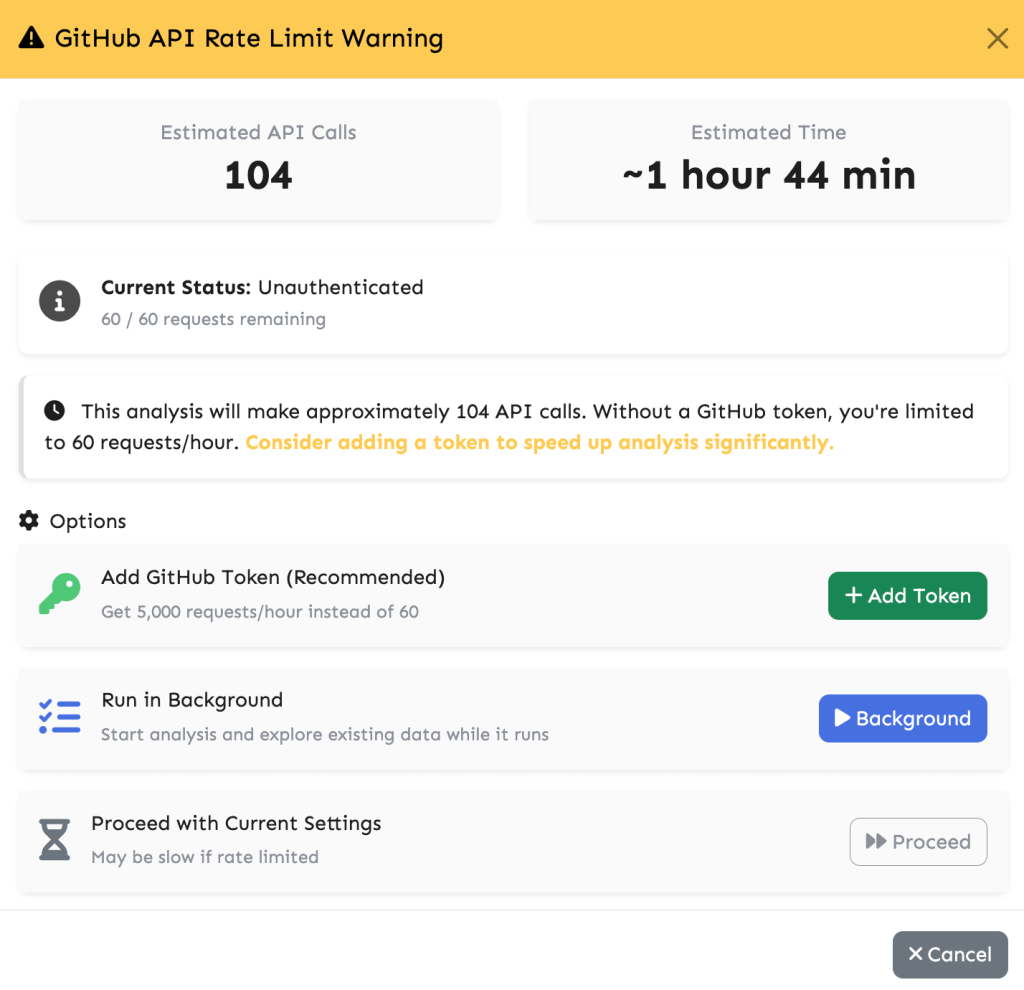
**Clear rate limit warnings**
**Explicit list of outbound hosts** for paranoid self-hosting or air-gapped deployment
Details: [https://cyfinoid.github.io/sbomplay/about.html#:~:text=Paranoid%20Self%2DHost%20/%20Airgapped%20Deployment](https://cyfinoid.github.io/sbomplay/about.html#:~:text=Paranoid%20Self%2DHost%20/%20Airgapped%20Deployment)
With that said Now its time for you to play with
## Links
- Live: https://cyfinoid.github.io/sbomplay/
- Source code: https://github.com/cyfinoid/sbomplay/tree/main
---
### GH Navigator Released: Full Coverage of GitHub’s Data and Control Planes
Date: 2025-09-23
URL: https://cyfinoid.com/gh-navigator-released-full-coverage-of-githubs-data-and-control-planes/
Today we are announcing the release of **[GH Navigator](https://cyfinoid.github.io/ghnavigator/)**. With this addition, alongside our existing **[KeyChecker](https://github.com/cyfinoid/keychecker/)** project, we now have practical coverage of both the **data plane** and the **control plane** of the GitHub environment.
## TL;DR
GH Navigator and KeyChecker work together to provide complementary visibility and testing coverage for GitHub. KeyChecker automates SSH key validation and repository access checks to assess the **data plane**. GH Navigator is a client-side repository browser and bulk token analyzer that inspects token validity and scopes to assess the **control plane**. Used together they give a practical, repeatable way to evaluate what an attacker can read and what they can change.
## Why think in planes
Grouping actions and privileges into two conceptual planes helps clarify attacker capabilities and defender priorities. For a deeper dive into this framing, see our earlier post: [Decouple and Conquer: Understanding Control and Data Planes Across Technology](https://cyfinoid.com/decouple-and-conquer-understanding-control-and-data-planes-across-technology/).
- Data plane: operations that read, change, or exfiltrate repository contents, artifacts, or secrets — for example, cloning private repos, downloading releases, or reading configuration files.
- Control plane: operations that change configuration or permissions — for example, creating tokens, modifying collaborators, changing repository settings, or adding webhooks.
Treat these as separate but related surfaces when designing tests and controls.
## How KeyChecker works (data plane)
KeyChecker automates the manual techniques security teams have used for years: extracting usernames from SSH connection metadata and validating whether an SSH key grants access to a repository by running `git ls-remote` and related checks. The tool uses a plugin architecture and currently supports multiple SaaS providers so it can be extended to more platforms in the future.
Key takeaways about KeyChecker:
- It converts raw SSH keys into reproducible tests that show exactly which repos a key can access.
- It exposes the true blast radius of a stolen key by automating enumeration and brute-force repository checks.
- It is intended for red teams, incident responders, and defensive validation within authorized engagements.
[We wrote a detailed blogpost](https://cyfinoid.com/automating-a-known-weakness-introducing-keychecker/) and also you can access the tool at [github](https://github.com/cyfinoid/keychecker/) or [pypi](https://pypi.org/project/keychecker/)
## How GH Navigator works (control plane)
GH Navigator is a pure client-side web application. Open `index.html` in a modern browser, paste a Personal Access Token (PAT), and the app runs entirely in-memory with no server component.
The project has two distinct parts:
- Navigator UI (repository views): a clean repository browser that lists organizations and repositories visible to the token and lets you view repository contents. It is focused on visibility and exploration. It does not modify settings and it does not enumerate permissions on its own.
- Token Validator (permissions map): a companion tool that validates a single token or a list of tokens, then queries GitHub to build a per-repository map showing what the token can do. Typical output includes whether the token is valid, token scopes, and for each repository the effective permission level such as read, triage, write, maintain, or admin.
Control plane insight comes from the **Token Validator** output, which summarizes what configuration or management actions are permitted for the token on each repository. The **Navigator UI** is for viewing what the token can see.
## Complementary workflow: data + control
Use KeyChecker and GH Navigator together for full coverage:
1. Use KeyChecker to validate SSH keys and enumerate which private repositories they can access. That reveals immediate data-plane exposure.
2. Use GH Navigator Token Validator to identify valid PATs, list their scopes, and produce a per-repository permission map.
3. Use Navigator UI to quickly open any repository that appears in the permission map to verify visibility and to audit contents as part of the assessment.
4. Correlate findings: if KeyChecker shows repo content is accessible and the Token Validator shows write, maintain, or admin permissions for the same repositories, treat that as high impact.
## Responsible use and limitations
Both tools are intended for legitimate security work. Rules of use:
- Obtain explicit authorization before testing keys or tokens you do not own.
- Do not perform destructive actions against systems you do not manage.
- Respect GitHub API rate limits and avoid creating noise that could resemble an attack.
Limitations:
- KeyChecker focuses on SSH and repository-level validation; it does not replace a full post-compromise investigation that captures other artifacts such as cached credentials, API tokens, or internal documentation leaks.
- GH Navigator depends on GitHub API responses and the token scopes provided by PATs; it cannot see actions that require elevated platform logging that the API does not expose.
## Closing thoughts
Recent malware campaigns have highlighted a consistent theme: attackers are stealing GitHub tokens and SSH keys directly from developer machines. Once exfiltrated, these credentials allow adversaries to pivot into both the data plane and the control plane of GitHub environments. Without a clear way to test exposure, defenders are left guessing what a leaked key or token might enable.
KeyChecker and GH Navigator change that equation. KeyChecker makes it practical to answer “what can be read?” while GH Navigator answers “what can be changed?” Together they let you gauge the potential impact of credential leakage and prioritize remediation.
Use both to produce reports that separate data-plane and control-plane impact and provide clear, prioritized remediation.
---
[Software Supply Chain](https://cyfinoid.com/research/software-supply-chain-security/) is one of our core research areas and we offer various trainings on this Domain. Below are some of our upcoming trainings.
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
1 August 2026 – 2 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
3 August 2026 – 4 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
### [Mastering Third-Party Risk Management : Vendor & Software Supply Chain BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
Date: 4 August 2026Las Vegas, USA[](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
---
### Decouple and Conquer: Understanding Control and Data Planes Across Technology
Date: 2025-09-23
URL: https://cyfinoid.com/decouple-and-conquer-understanding-control-and-data-planes-across-technology/
---
### Introduction: Lessons from Networking
In networking, the separation of the control plane and data plane is foundational. The data plane moves packets from point A to point B, while the control plane makes decisions such as routing, path selection, and policy enforcement.
This separation was intentional. It provided resilience, modularity, and security. Each plane could be optimized or attacked independently, unless the integration point (such as BGP route injection) was mishandled.
The same thinking applies far beyond networking. Yet in many domains, we either ignore it or unknowingly mix the two. When the control and data layers are conflated, visibility drops, attack surfaces expand, and accountability is muddled. This piece explores where similar patterns exist in modern systems, why separation matters, and how it can reshape our threat modeling.
---
### Key Examples of Control and Data Planes Beyond Networking
#### Git and GitHub (Version Control)
- Data Plane: Git repositories (code, history, commits).
- Control Plane: GitHub/GitLab/Bitbucket web UIs, permissions, CI/CD triggers.
> **Why it matters**: A compromised GitHub token may not breach the Git server directly, but it can manipulate access, inject code, and trigger builds silently.
**[Case Study: Shai Hulud Worm](https://jfrog.com/blog/shai-hulud-npm-supply-chain-attack-new-compromised-packages-detected)** — A worm-like malware actively hunted for GitHub tokens. Using compromised control tokens, it created repositories, exposed private repos, and attempted to steal secrets, all without directly breaching Git data.
#### GitHub SSH vs Token Blindspots
- Data Plane: Git operations using SSH keys.
- Control Plane: GitHub tokens, web UI, and associated monitoring.
> **Why it matters**: While GitHub provides excellent visibility and logging for token usage, monitoring for SSH key based activity is far less transparent to regular users. This creates a blind spot where data plane operations may occur without the same level of auditability.
[**Case Study: **keychecker](https://cyfinoid.com/automating-a-known-weakness-introducing-keychecker/) We release this tool based on our research that there is no publicaly or freely available logging for the actions done by ssh key. We weaponized this by creating a username detection as well as private repository bruteforcing tool. SSH keys could exfiltrate or manipulate repositories without triggering the same detailed logs available for token-based access. This asymmetry highlights the importance of balanced observability across both authentication methods.
#### AWS Console and EC2 (Cloud Infrastructure)
- Data Plane: EC2 VMs, EBS volumes, S3 buckets.
- Control Plane: AWS Console, IAM, CloudFormation APIs.
> **Why it matters**: A VM may have its own security, but access to the AWS Console can stop, modify, or snapshot it instantly. The true blast radius often lies at the control level.
**[Case Study: Scattered Spider](https://en.wikipedia.org/wiki/Scattered_Spider)** – Attackers used social engineering to gain access to cloud admin accounts, bypassing MFA and escalating control plane access. With console-level control, they halted services and accessed sensitive data without breaching workloads directly.
#### Kubernetes and Containers (Cloud-Native World)
- Data Plane: Pods, containers, network traffic.
- Control Plane: Kubernetes API server, scheduler, etcd.
> **Why it matters**: Access to the API server can reroute services, inject containers, or escalate privileges across the cluster without exploiting individual apps.
[**Case Study: Ingress-nginx CVE-2025**-1974 ](https://kubernetes.io/blog/2025/03/24/ingress-nginx-cve-2025-1974)— Multiple research reports highlighted open Kubernetes dashboards discovered in cloud environments. Attackers leveraged exposed APIs to deploy cryptominers, demonstrating how control-plane compromise can bypass hardened container workloads.
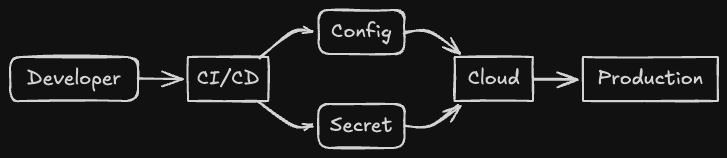
#### CI/CD Pipelines and Build Artifacts (DevOps)
- Data Plane: The code being built and the artifacts produced.
- Control Plane: The pipeline configuration, runner permissions, webhook triggers.
> **Why it matters**: A poisoned pipeline definition can introduce backdoors into every software release.
**[Case Study: XZ Utils Backdoor](https://en.wikipedia.org/wiki/XZ_Utils_backdoor)** — Attackers compromised a critical open-source project by tampering with its build process. Control of the pipeline allowed insertion of malicious code into distributed binaries, showing how CI/CD control-plane compromise bypassed direct code review.
#### Emerging Domain: ML Pipelines
- Data Plane: Training datasets, model weights.
- Control Plane: MLflow servers, training orchestration scripts.
> **Why it matters**: Attacking the control system that governs training jobs can produce poisoned or biased models, even when the raw data remains untouched.
**[Case Study: LLM Supply Chain Attacks 2025](https://genai.owasp.org/llmrisk/llm032025-supply-chain)** — Research demonstrated poisoning through ML orchestration layers. By compromising retraining pipelines, attackers introduced subtle manipulations into large language models without directly altering raw training data.
---
### When Planes Collide: Hidden Complexity
In many systems, data and control planes are not clearly separated. Sometimes they blend by necessity, sometimes by oversight. This overlap creates fertile ground for subtle security gaps and operational failures.
Common symptoms:
- Developers using production credentials in CI builds.
- Terraform applying changes to live infrastructure with no approval loop.
- Admin interfaces that allow both configuration and direct data manipulation.
**Fixing It**: Introduce approvals, reduce cross-plane permissions, and isolate CI agents from direct data access. Treat each bridge as a security boundary.
---
### Threat Modeling: Planes and Integration Points
Instead of one flat threat model, think in three layers:
- Data Plane Threats: Direct attacks such as data corruption or unauthorized access.
- Control Plane Threats: Configuration tampering or privilege escalation.
- Integration Point Threats: Tokens, API keys, and session handling that bridge the two.
### Signs You Have Blind Spots
- Lack of distinct audit logs for configuration and runtime actions.
- Shared or reused credentials across deployment and operations.
- Absence of multi-factor authentication on CI/CD or admin tools.
- Monitoring limited to resource metrics without tracking configuration changes.
- Privileged API keys stored insecurely or used across multiple services.
These patterns often point to weak integration boundaries between control and data planes. A practical example is GitHub SSH access: token usage is logged extensively, but SSH key activity is less visible to end users. This creates a data plane blind spot that attackers can exploit without triggering the same monitoring controls.
---
### Practical Advice: Start Thinking in Planes
- Design: Sketch control and data separately. Identify meeting points and who controls what.
- Threat Model: Independently ask: What if control is compromised? What if data is corrupted?
- Operate: Treat control plane activity such as admin console logins as higher sensitivity events than routine data plane activity.
- Audit: Ensure logs capture control actions distinctly from data access events.
Many catastrophic breaches happen not because one plane was ignored, but because either control or data was left exposed or misunderstood. Both must be treated as equally important and capable of being attacked separately.
---
### Closing Thought
In complex systems, everything may appear interconnected. Clarity comes from deliberately separating control from data and modeling them both independently and together.
Failures do not usually arise because one plane is inherently weak. They occur when the integration points between the two are overlooked, or when either control or data is undervalued. Both planes represent distinct attack surfaces and both deserve equal attention in design, operations, and monitoring.
**Start seeing the world in planes, and secure each one on its own terms.**
---
[Software Supply Chain](https://cyfinoid.com/research/software-supply-chain-security/) is one of our core research areas and we also offer various trainings on this Domain. Below are some of our upcoming trainings.
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
1 August 2026 – 2 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
3 August 2026 – 4 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
### [Mastering Third-Party Risk Management : Vendor & Software Supply Chain BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
Date: 4 August 2026Las Vegas, USA[](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
---
### Automating a Known Weakness: Introducing keychecker
Date: 2025-08-22
URL: https://cyfinoid.com/automating-a-known-weakness-introducing-keychecker/
For the past three years, whenever we’ve talked about [supply chain security in trainings and conference talks](https://cyfinoid.com/research/software-supply-chain-security/), one slide always stood out: the risk of **developer workstation compromise**. Among the easiest and most valuable loot from such an incident? **SSH keys**. With a single stolen key, an attacker can often pivot into private repositories, escalating from one developer’s machine to the entire organization.

This idea has been floating around in theory for years. Today, we’re releasing `keychecker` — a tool that automates what we’ve been teaching manually: **taking a suspicious key, validating where it works, and mapping its scope of impact**.
---
## Why `keychecker`?
The concept is simple:
- SSH connections leak metadata — even without full access, they can expose the associated username.
- Running git ls-remote against a private repo can confirm whether a key is valid for that target.
These two primitives form the backbone of the tool. `keychecker` just makes them repeatable, automatable, and extendable.
Currently, the tool supports **six SaaS services** (see README) through a **plugin-based architecture**, meaning it can be extended to support more providers in the future.
This isn’t rocket science. It’s just codifying the obvious so teams can move past the *idea* of “keys get stolen” and start validating the *impact* of that theft.

---
## A Tool With Two Audiences
### For Red Teamers
Red teamers know that post-exploitation is about *showing impact*. Looting a developer machine and finding SSH keys is one thing; demonstrating that those keys open doors into sensitive repos is what gets executive attention.
With `keychecker`, you can:
- Test stolen or simulated keys against multiple SaaS providers.
- Automate brute-forcing repository access without guesswork.
- Turn raw loot into a clear story: “Here’s the blast radius of this one stolen key.”
### For Blue Teamers
Blue teams rarely get the chance to ask: *“If one of our developer’s keys were stolen, what could it actually reach?”*
`keychecker` provides a way to:
- Validate the scope of exposure tied to a key.
- Run internal simulations to identify weak points before attackers do.
- Build more realistic threat models around key compromise scenarios.
In other words, it’s both a **scope identifier** and a **gap-finder**.
---
## The Telemetry Blind Spot
One reason this problem has persisted is the lack of visibility. GitHub, GitLab, Bitbucket, and others don’t consistently expose failed SSH key attempts in their logs. For defenders, that means there’s almost no telemetry around brute-force attempts. <[https://github.com/settings/security-log](https://github.com/settings/security-log)> is the security log that is offered by github and it doesnt list ssh key attempts.
Attackers operate in this dark space. `keychecker` shines a small light by making the testing process transparent and reproducible for defenders as well.
---
## Responsible Use
Like most post-exploitation helpers, this is not a tool for opportunistic abuse. It’s meant for:
- Red team engagements (to demonstrate impact).
- Incident response (to scope blast radius of stolen keys).
- Defensive validation (to proactively understand risks).
Use it in controlled environments, not against random targets.
---
## What’s Next
`keychecker` is only one piece of the puzzle. Developer workstation compromise often comes with more loot than just keys: API tokens, cached credentials, internal documentation (Confluence, Jira, etc.). Future iterations of the tool could integrate these data points to simulate real-world lateral movement more fully.
But for now, it closes a gap that has existed for far too long.
---
## Get the Tool
🔗 [GitHub: cyfinoid/keychecker](https://github.com/cyfinoid/keychecker)
If you’re training, red-teaming, or building defenses against software supply chain risks, `keychecker` is a small but sharp addition to your toolkit.
---
[Software Supply Chain](https://cyfinoid.com/research/software-supply-chain-security/) is one of our core research areas and we offer various trainings on this Domain. Below are some of our upcoming trainings.
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
1 August 2026 – 2 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
3 August 2026 – 4 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
### [Mastering Third-Party Risk Management : Vendor & Software Supply Chain BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
Date: 4 August 2026Las Vegas, USA[](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
---
---
### Introducing 3P-Tracer: third-party mapping in your browser
Date: 2025-07-29
URL: https://cyfinoid.com/introducing-3p-tracer-third-party-mapping-in-your-browser/
**TL;DR** 3P‑Tracer is a browser‑first recon tool that helps you see which third‑party services a domain relies on. It runs on the client side, uses DNS over HTTPS and certificate transparency, classifies common providers, and highlights email security posture. No logins, no API keys, nothing leaves your machine.
> Live tool: [3P‑Tracer](https://cyfinoid.github.io/3ptracer/)
> Code: [GitHub repository](https://github.com/cyfinoid/3ptracer)
> About: [How it works](https://cyfinoid.github.io/3ptracer/about.html)
---
## Why we built this
Modern recon often begins with a simple question: what does this domain talk to. Many teams still reach for heavyweight setups or rate‑limited SaaS. We prefer a simpler path that lowers the barrier to entry. This is part of our ongoing effort to put capable security tooling in the browser so people can start in seconds and keep their data local. For the thinking behind this approach, read: [Making Security Tools Accessible: Why I Chose the Browser](https://blog.anantshri.info/making-security-tools-accessible-why-i-chose-the-browser/).
## What 3P‑Tracer does
- Comprehensive DNS analysis Live DoH queries for A, AAAA, CNAME, TXT, MX, NS, SPF, and DMARC.
- Certificate Transparency discovery Surfaces historical and shadow subdomains using CT logs.
- Service detection and classification Flags common providers across clouds, CDN and hosting, DNS, email, and security services.
- Security checks that matter DMARC policy parsing, SPF insights, a quick risk view.
- Rich output CNAME maps, categorized services, historical records, subdomain lists, and quick stats that make reporting easier.
> Optional visuals to insert here:
>
> 1. Screenshot of the main results view.
> 2. CNAME mapping diagram.
> 3. Email posture summary card.
## Privacy by design
3P‑Tracer is a static web app. Analysis happens in your browser. We do not collect targets or results. DNS queries use encrypted DoH. The code is open for review under the MIT license.
## Who it is for
- OSINT and recon Quick third‑party mapping before a deeper pass.
- Blue teams Inventory external dependencies and email posture without opening tickets.
- Developers Fast sanity check of what a domain exposes and which vendors it leans on.
## How it works at a glance
1. Query DNS for core records, including SPF and DMARC, using multiple DoH providers.
2. Enumerate subdomains with certificate transparency and passive sources.
3. Classify services using CNAME targets, IP ranges, and known provider patterns.
4. Run safety checks for DMARC policy and basic takeover signals, then render structured results.
## Quick start
1. Open the live app: 3P‑Tracer
2. Enter the domain you want to check
3. Review the DNS, CT, and service classification sections
4. Download / Save the page or copy/paste results into your notes or report
5. If you find gaps or rough edges, file an issue on the repo
## Roadmap
- Deeper provider fingerprints and heuristics.
- Subdomain takeover detection signals
- Export options for JSON and CSV
If any of these would unblock your workflow, comment on or upvote the matching GitHub issue or create an issue if nothing matches.
## Reliability and limits
3P‑Tracer relies on public data sources. Some endpoints rate limit or change behavior. If you see incomplete sections, try again later or open an issue with details and a sample domain that you own. The About page lists current data sources and caveats.
## Responsible use
Understand that we are not hunting for data, we are simply accumulating the data that is already public. Treat output as a starting point for analysis. Validate findings before acting on them. Our tool doesn’t uncover anything hidden, we simply list out what everyone else in the world can see.
## Thanks
This work builds on the generosity of the open web and the teams that expose DoH, CT, and passive DNS data. It also builds on our belief that good security tools should be easy to start and easy to reason about.
---
SelfPromotion>
[Software Supply Chain](https://cyfinoid.com/research/software-supply-chain-security/) and [Cloud Security](https://cyfinoid.com/research/cloud-security/) are our core research areas and we also offer various trainings on this Domain. Below are some of our upcoming trainings.
### [Attacking Cloud Environments (AWS, Azure, GCP, DigitalOcean and Aliyun) BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-51037)
1 August 2026 – 2 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-51037)
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
1 August 2026 – 2 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
### [Attacking Cloud Environments (AWS, Azure, GCP, DigitalOcean and Aliyun) BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-510371770400827)
3 August 2026 – 4 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-510371770400827)
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
3 August 2026 – 4 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
### [Mastering Third-Party Risk Management : Vendor & Software Supply Chain BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
Date: 4 August 2026Las Vegas, USA[](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
---
### Introducing SBOM Play: A Privacy-First SBOM Explorer with Vulnerability & License Insights
Date: 2025-07-17
URL: https://cyfinoid.com/introducing-sbom-play-a-privacy-first-sbom-explorer-with-vulnerability-license-insights/
**SBOMs (Software Bill of Materials)** have become a key asset in managing software supply chain risks. But despite the buzz, many teams still find it hard to start using SBOMs meaningfully—especially without installing complex tools or giving up control over their data.
We wanted to change that. So we built something lightweight, usable, and privacy-respecting.
### 💡 Meet **SBOM Play**
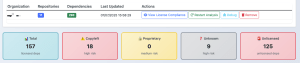
**SBOM Play** is a simple yet powerful browser-based tool to visualize and explore SBOMs. It adds essential context like **vulnerability data**, **license analysis**, and **component trends**—with zero setup required.
🧠 Think of it as your **SBOM viewer with superpowers**, made for developers, researchers, and security teams alike.
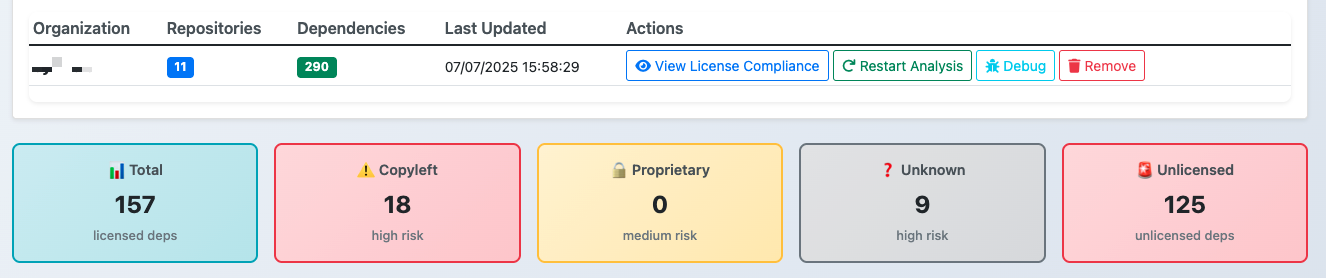
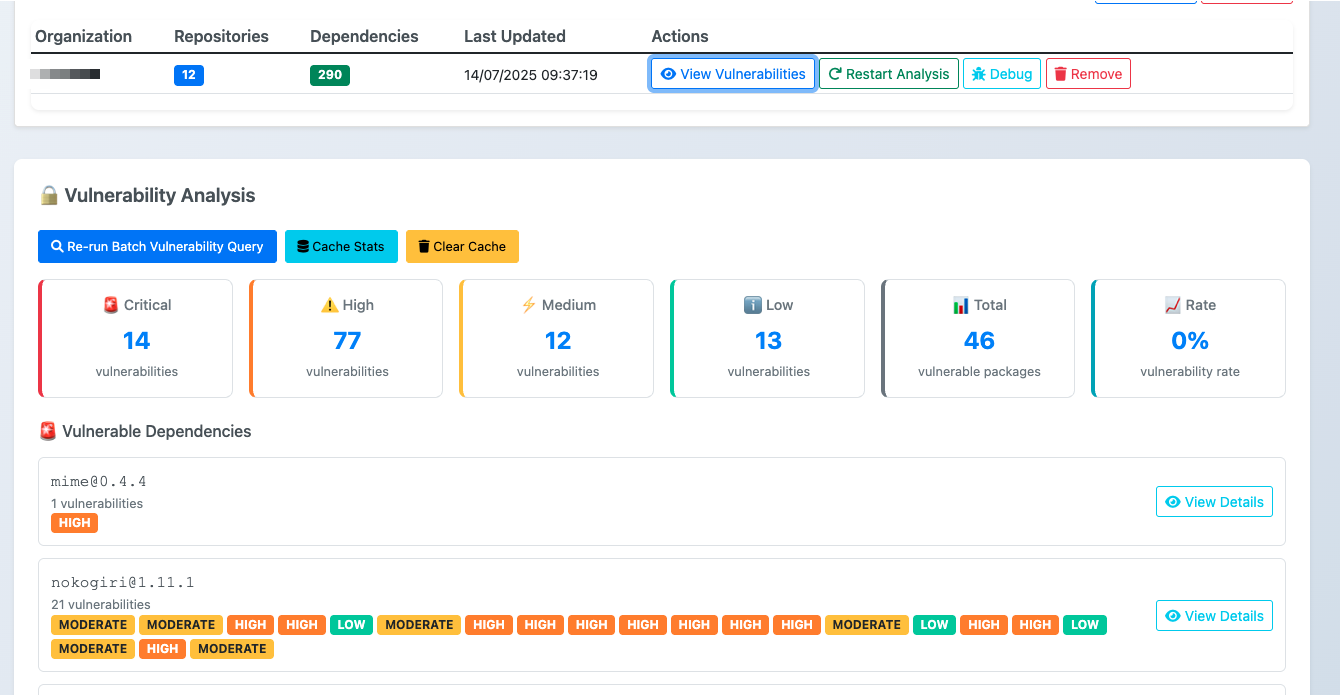
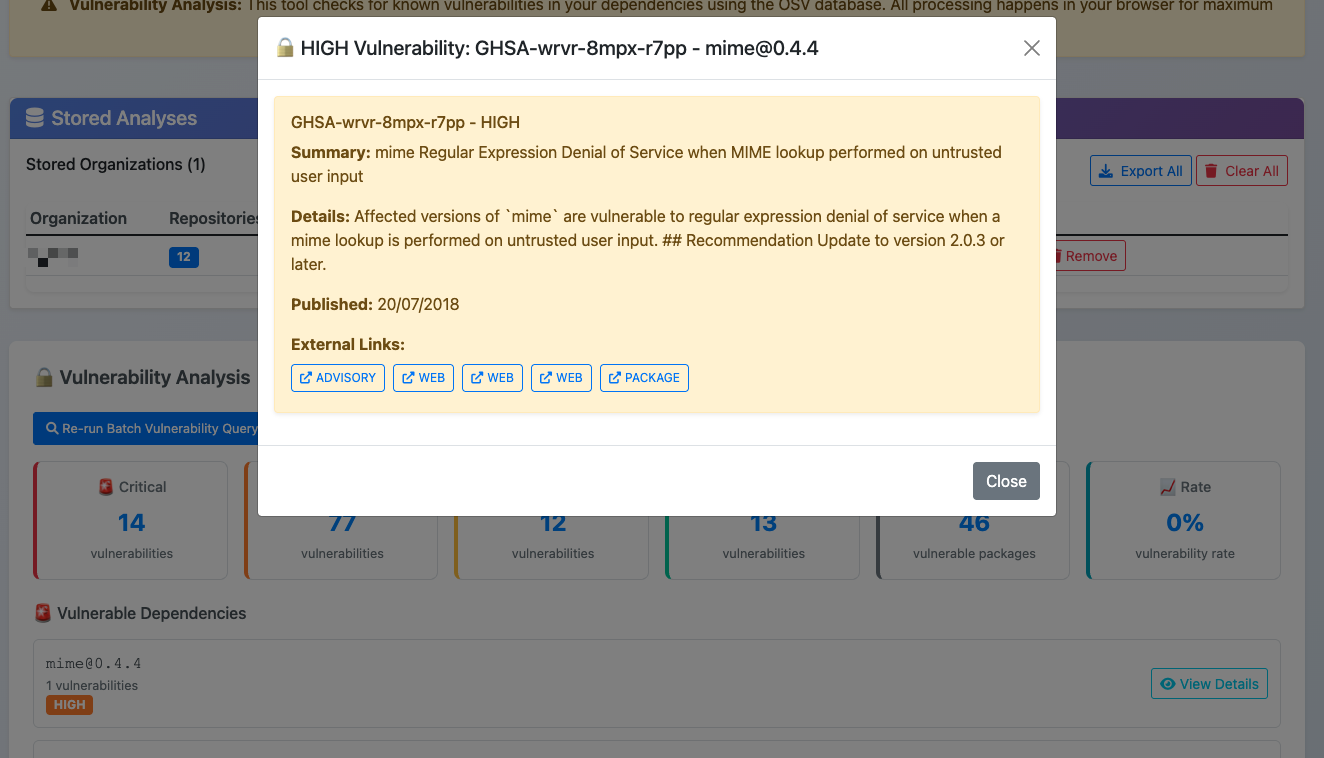
### SBOM Play in Action
Project Banner

Statistics Dashboard

Dependency View
Code License Distribution
Vulnerability Listing
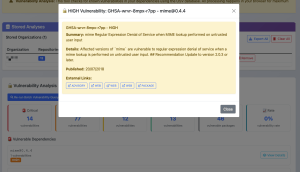
Individual Vulnerability View



---
### 🚀 Key Features
- ✅ Dependency Graphs Across Repos: Understand which third-party packages appear across multiple repositories
- 🔁 Major & Minor Dependency Trends: Spot commonly reused dependencies and high-risk packages
- 📜 License Breakdown: Identify components with missing, non-compliant, or incompatible licenses
- 🏢 Cross-Organization Insights: Compare SBOMs across multiple orgs to see systemic patterns
- 🛡️ Vulnerability Mapping: View which packages bring in the most known CVEs
- 🔐 Privacy by Design: 100% client-side—no data leaves your browser
---
### 🔍 How It Works
No backend. No tracking. No servers required
SBOM Play is a **pure HTML + JavaScript** tool that runs entirely in your browser. All processing happens locally using `localStorage` for data handling. This means:
- You don’t need to upload files anywhere
- Your analysis is yours alone
- You can inspect the code or deploy it locally
---
### 📂 Open Source & Ready to Use
- GitHub Repository: https://github.com/cyfinoid/sbomplay
- Live: https://cyfinoid.github.io/sbomplay/
We believe in building **transparent, inspectable tools** so the entire codebase is open source under the [MIT License].
---
### 🛠️ What’s Next?
This is just the beginning. We’re already working on:
- 📦 SBOM merging across multiple sources
- 📈 Time-series trends of dependency shifts
- 🔄 Exportable reports & visualizations
- ⚙️ CI-compatible integrations for automated SBOM review
Got ideas or feature requests? [Open an issue on GitHub](https://github.com/cyfinoid/sbomplay/issues) or [connect with us](https://cyfinoid.com/contact/).
---
### 🔗 Explore Now
> 👉 [Try SBOM Play in your browser](https://cyfinoid.github.io/sbomplay/)
> 🔍 [Check out the source code](https://github.com/cyfinoid/sbomplay)
Whether you’re a developer exploring your stack, a security engineer doing due diligence, or a privacy-conscious open-source user—**SBOM Play is built for you.**
[Software Supply Chain](https://cyfinoid.com/research/software-supply-chain-security/) is one of our core research areas and we also offer various trainings on this Domain. Below are some of our upcoming trainings.
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
1 August 2026 – 2 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
3 August 2026 – 4 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
### [Mastering Third-Party Risk Management : Vendor & Software Supply Chain BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
Date: 4 August 2026Las Vegas, USA[](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
---
### Cyfinoid Research at Hacker Summer Camp 2024
Date: 2024-07-30
URL: https://cyfinoid.com/cyfinoid-research-at-hacker-summer-camp-2024/
Hackersummercamp USA is an annual gathering of hackers (read infosec professionals / researchers, plain old hackers all encompasing) in the desserts of Nevada at sin city Las vegas.
This year is nothing different, you have BlackHat 2024, DEFCon 32, Bsides Las Vegas as the three main pillars and lots of other conferences and parties happening on the sides.
Cyfinoid Research since its inception has been present at these events in various capacities and we continue the tradition this year also. This year cyfinoid research’s calender of activity looks like this.
1. We are continuing with our “Attack and Defend Android Applications” class and we have two rounds of that class available in Virtual mode 3-4 Aug and 5-6 Aug
2. We have introduced our Multi Cloud Hacking class for the first time in BlackHat title Going beyond shells! – Hacking AWS, Google Cloud, DigitalOcean and Aliyun (Virtual)Dates: Again available in virtual mode on August 3-4, 2024, and August 5-6, 2024
3. Our Founder “Anant Shrivastava” would be moderating a Birds of feather discussion ”Security Champions Meetup” with panelists including Dustin Lehr, Kymberlee Price, Tanya Janca.
4. Anant will also be representing Review Board for Mobile Track Meetup
5. Anant is one of the organizer for Hackathon event at Recon Village : August 9-10, 2024
Cyfinoid is based on research and what better way to celebrate research then to spotlight the must attend talks from this year’s BlackHat USA 2024 Program.
Following are the sessions we thing you should take time to attend physically or if not possible watch the video As soon as they appear in the blackhat App.
- Cracking the 5G Fortress: Peering Into 5G’s Vulnerability Abyss by Kai Tu, Yilu Dong, Abdullah Al Ishtiaq, Syed Md Mukit Rashid, Weixuan Wang, Tianwei Wu, Syed Rafiul Hussain
- The Way to Android Root: Exploiting Your GPU on Smartphone by Xiling Gong, Xuan Xing, Eugene Rodionov
- Attacking Samsung Galaxy A* Boot Chain, and Beyond by Maxime Rossi Bellom, Raphael Neveu, Damiano Melotti, Gabrielle Viala
- Use Your Spell Against You: Threat Prevention of Smart Contract Exploit By Reusing Opcode Trace by Yajin Zhou
- Listen to the Whispers: Web Timing Attacks that Actually Work by James Kettle
- Kicking in the Door to the Cloud: Exploiting Cloud Provider Vulnerabilities for Initial Access by Nick Frichette
- The GCP Jenga Tower: Hacking Millions of Google’s Servers With a Single Package (and more) by Liv Matan
- Self-Hosted GitHub CI/CD Runners: Continuous Integration, Continuous Destruction by Adnan Khan, John Stawinski
While these are some of our favourite talks from BlackHat Only our founder [Anant Shrivastava has outlines his personal favourite talks from other conferences also in his blog](https://blog.anantshri.info/hacker-summer-camp-2024-black-hat-defcon-and-beyond/).
Hoping to see you in Vegas, and if you want to connect feel free to connect with us via contact form or over at [Linkedin](https://www.linkedin.com/company/cyfinoid/) or Connect with [Anant Shrivastava](https://linkedin.com/in/anantshri)
---
### Enhancing Open Source Security for Startups with Automated Scanning
Date: 2023-09-19
URL: https://cyfinoid.com/enhancing-open-source-security-for-startups-with-automated-scanning/
Startups often rely heavily on open source software to accelerate development, minimize costs and leverage the extensibility they offer. However, this reliance can also expose them to supply chain risks, such as vulnerabilities in the software they depend on along with source threats, build threats and dependency threats. While startups have alignment towards a specific goal these dependencies that they gather in the process may not be aligned to the same goals, a lot of them might be hobby projects or code made opensource to showcase the capabilities and maintaining them might not be a priority for the developers. Since this is unpaid work expectation of maintenance and upkeep is not the right thing to have from the OSS maintainers.
This puts the organisations at a risky spot, using these dependencies help accelerate the development but it effectively puts the “burden” on the startups for ensuring the safety of this code also. To mitigate these risks, it’s crucial for startups to establish a basic security scanning process. With the current world of SaaS platforms offering lots of free services for startups and smaller teams, there is really no excuse left for startups to not setup a baseline code scanning setup we are not just suggesting setting up a code scanning service for your own code but also for your dependencies.
In this blog post, we will explore how to set up a simple and effective scanning capability using GitHub, GitHub Actions, and various security tools, to give startups more confidence in their open source software choices. What we are showing in this blog post should be treated as a guidance and orgs can focus on deploying this on their own CI / CD environments, Github is just a system we choose to demonstrate the concept. GitHub has implemented some security features related to scanning repositories for potential vulnerabilities. These features are often provided by third-party services integrated into GitHub Actions workflows. We will also discuss how GitHub Actions can be employed by companies to enhance security in various ways including automated code scanning, creating CI pipelines that run tests and checks, enforcing security checks on pull requests and also enforcing security compliance standards. We will also discuss the benefits, pitfalls, and best practices for approaching software with identified bugs and interpreting their severity.
Github is a sought after web based version control platform which offers collaborative software development. It allows hosting and sharing code repositories, including open source projects. By utilizing GitHub Actions, startups can automate tasks like code scanning, dependency updates and vulnerability scanning, minimize the risk of malicious code impacting the host environment or other workflows through container isolation, and manage access control. GitHub allows you to perform code scanning through multiple methods: utilizing GitHub Actions, integrating it with your continuous integration (CI) system, or running it directly on GitHub itself. Both the basic and advanced configurations for code scanning are available through GitHub Actions. With the default setup, the system automatically determines the programming languages to analyze, the query suite to execute, and the events that should trigger the scans. However, if you prefer, you have the option to manually choose the query suite and languages to be analyzed within the default setup.
For more advanced customization, you can opt for the advanced setup, which offers further options to tailor your code scanning workflow. CodeQL analysis is one of the types of code scanning available on GitHub, but you can also find other code scanning workflows in the GitHub Marketplace that you can utilize for your projects.
### **Github Action**s 101
To get started with automated scanning, you’ll need to set up a GitHub Actions workflow in your project repository. This workflow will trigger the scanning process every time there is a push or a pull request. In this section, we will walk you through the necessary steps to create and configure a simple GitHub Actions Workflow.
To set up a workflow, you can follow these steps:
1. Set up Actions in your repository: Log In to your GitHub account and navigate to your GitHub repository for which you want to setup Github Actions. Click on Actions.

1. Create a workflow: In the next page that appears, click on Configure in order to setup a workflow.

1. Generate and configure the YAML file: You will be able to see a yaml file, you can also customize this file if you want to. If you want to use the default yaml file for setup, simply click on Configure.

You have configured a basic GitHub actions workflow. This process was manual as of now however this can be automated as lots of github action workflows are pre-created by GitHub and made available for direct usage. We will leverage this workflow process to setup different scanning softwares in next section.
### **Integrating Security Scanning Tools**
Next, we will discuss integrating various security tools into your GitHub Actions workflow. These tools will help you identify not only known vulnerabilities but also code quality issues that might lead to potential security risks. Integrating security tools into GitHub Actions can help ensure that your code adheres to compliance and make auditing processes smoother. Some common tools to consider include:
#### **CodeQL:**
CodeQL is a powerful tool developed (acquired and enhanced) by Github, which allows developers to identify and eliminate security vulnerabilities in their code. It performs such tasks only if the open source codebase is available on GitHub. Furthermore, in order to test the codebase should be released under an OSI-approved open source license.
**Key Features:**
- CodeQL allows developers to write custom queries to find specific issues in the code.
- It also maintains a resource pool of open source projects and their vulnerability history that serves as a valuable resource into known vulnerabilities.
- CodeQL provides early detection if it is integrated into a project’s continuous integration pipeline.
**Requirements for using default setup:**
1. The code should include at least one of the CodeQL supported languages excluding Swift.
2. Github Actions should be enabled.
3. It should be publicly visible.
**Configure default setup for code scanning:**
You can configure the default set up by following steps:
1. Navigate to your github repository for which you want the default setup.
1. Under your repository name, click on Settings.

1. In the Security section of Settings, click on Code Security and Analysis.

1. Navigate to the Code Scanning section and click on Set up, then click on Default.
1. You can also customize the code scanning setup by clicking on the Edit option.
1. Review the settings and then click on Enable CodeQL.
The CodeQL setup configuration is now done.
#### **Semgrep**
Semgrep is a fast, open-source, static analysis tool for finding bugs and enforcing code standards. It is a rule-based tool, which means that it uses patterns to match specific code constructs. This makes it very flexible and powerful, as it can be used to find a wide variety of bugs and issues.
Here are some of the benefits of using Semgrep:
- Fast: Semgrep is very fast and can scan large codebases in a matter of minutes.
- Accurate: Semgrep is very accurate and can find a wide variety of bugs and issues.
- Easy to use: Semgrep is easy to use and can be used by developers with no prior static analysis experience.
- Flexible: Semgrep is very flexible and can be used to find a wide variety of bugs and issues.
- Extensible: Semgrep is extensible, and new rules can be easily created.
At Cyfinoid we are big fans of Semgrep. By utilizing Semgrep and GitHub Workflows, we can automate the detection of coding vulnerabilities. To achieve this, we will create the following workflow:
1. The workflow is designed to perform a scan of your application’s entire codebase, offering a comprehensive analysis of its contents.
1. To set up this workflow, copy and paste the following content into the .github/workflows/semgrep-full.yaml file:
```
---
name: Semgrep Full Scan
on:
workflow_dispatch:
push:
branches:
- main
schedule:
- cron: '0 1 * * 6'
jobs:
semgrep-full:
permissions:
contents: read # for actions/checkout to fetch code
security-events: write # for github/codeql-action/upload-sarif to upload SARIF results
runs-on: ubuntu-latest
container:
image: returntocorp/semgrep
steps:
# step 1
- name: clone application source code
uses: actions/checkout@v3
# step 2
- name: full scan
run: |
semgrep \
--sarif --output report.sarif \
--metrics=off \
--config="p/default"
# step 3
- name: save report as pipeline artifact
uses: actions/upload-artifact@v3
with:
name: report.sarif
path: report.sarif
# step 4
- name: publish code scanning alerts
uses: github/codeql-action/upload-sarif@v2
with:
sarif_file: report.sarif
category: semgrep
```
Note: This workflow is not fully hardened there is a lot more that can be done to harden the workflow. We will write another blogpost covering hardening techniques for specific workflows.
1. Afterward, you can manually initiate this workflow to execute the initial full scan. All detected issues will be displayed in the Code Scanning alerts, accessible within the Security tab of your GitHub repository.

#### **Language-Specific Tools**
Based on the programming languages utilized in your project, you might consider incorporating specialized tools designed specifically for each language.Source code analysis tools or Static Application Security Testing (SAST) Tools, are designed to examine your source code or compiled code to uncover security issues. These tools can be integrated into your development environment, assisting you in identifying problems while writing software. By using SAST tools, you can save valuable time and effort, as they catch vulnerabilities early on, preventing the need to address them later in the development process.OWASP even has a list of SAST tools that can be used for various languages. All the listed tools can be explored via the mentioned link: [https://owasp.org/www-community/Source_Code_Analysis_Tools](https://owasp.org/www-community/Source_Code_Analysis_Tools)
### **Additional Github’s Security setup**
#### ** Secret Scanning and Push Protection**
Lately the major hacks dont happen coz. of the buggy code but more coz someone accidentally let loose a secret. So can something be done about that. To avoid the fraudulent use of secrets that were accidentally disclosed, GitHub searches repositories for recognized categories of secrets. GitHub searches a repository’s contents for secrets that match patterns predefined by service providers when you activate secret scanning for a repository or push commits to a repository with secret scanning enabled. When a new partner pattern is introduced or changed, GitHub additionally does a scan of all past code content in public repositories with secret scanning turned on.
In order to enable secret scanning, follow the underlying steps:
1. Navigate to the repository where you want to enable secret scanning.
2. Click on the Settings tab located on the right-hand side of the repository’s menu.
3. From the settings menu, choose the Code Security & Analysis section.
4. In the Code Security & Analysis section, you’ll find an option for Secret scanning. Click on it.
5. Save changes to enable the secret scanning functionality.
After you’ve enabled secret scanning, GitHub will automatically scan your repository’s codebase for known patterns of secrets. If any secrets are detected, you will be notified through the configured channels. This proactive security measure helps prevent the inadvertent exposure of sensitive information and enhances the overall security of your software projects. This is not a foolproof solution but a good first step. This should ideally be augmented by code scanning software added to GitHub workflow as a secondary tool also.
#### GitHub push protection
GitHub push protection is a security feature provided by GitHub to prevent unauthorised or accidental changes to important branches of a repository. It helps maintain the integrity and stability of critical branches by requiring additional checks and approvals before any code changes can be pushed to those branches.
Push protection is particularly useful for branches like “main,” “master,” or other long-lived branches where the main development or production code resides. It prevents scenarios where code could be introduced without proper code review or testing, reducing the risk of introducing bugs, vulnerabilities, or breaking the application.
You can enable GitHub push protection for enterprise, organisation or repository. In order to enable the Push Protection for any of these, you can follow the link below:
[https://docs.github.com/en/enterprise-cloud@latest/code-security/secret-scanning/push-protection-for-repositories-and-organizations](https://docs.github.com/en/enterprise-cloud@latest/code-security/secret-scanning/push-protection-for-repositories-and-organizations)
### **Handling Results of Scan**

Scan report analysis is often the most ignored step. GitHub itself provides a nice dashboard for this to work however if there are cross platform tools in place then it might be a good idea to leverage third party dashboards. In order to efficiently work on the security issues identified we recommend leveraging Vulnerability aggregation software like ArcherySec / DefectDojo. These specialised softwares provide more comprehensive tooling to work on the vulnerability remediation.
Defect Dojo DashBoard
ArcherySec DashBoard
### Pitfalls to watch out for
While automated scanning presents numerous advantages, it is essential to be mindful of potential drawbacks:
1. False positives: Scanning tools may produce inaccurate alerts, necessitating manual assessment for validation. To minimize such occurrences, adjust the scanning rules and concentrate on the most pertinent issues.
2. Interpretation of results: Not all vulnerabilities carry equal risk. Startups must consider the vulnerability’s context, such as its location in the code and its usage, to determine its severity and prioritize accordingly.
3. Dependency on scanning tools: Relying solely on automated scanning can lead to a false sense of security. It is crucial to complement scanning with other security measures, like code reviews and secure development training, for comprehensive protection.
### **Approaching Software with Identified Bugs**
If your scanning procedure detects bugs or vulnerabilities, adhere to these recommended approaches:
1. Assess the risk: Assess the seriousness and potential consequences of the identified problem, considering your unique usage scenario and surroundings.
2. Prioritize fixes: Concentrate on resolving the most crucial vulnerabilities initially, prioritized according to their risk assessment.
3. Engage the community: In the case of an issue within an open source project, report the vulnerability to the project maintainers and contribute to the resolution process whenever possible. Contribution doesn’t necessarily means code contribution you can help by providing documentation and most importantly monetary support to a project that is helping you in your commercial venture.
4. Monitor for updates: Monitor for updates and patches pertaining to the affected software, and apply them promptly upon availability.
For startups that depend on open source software, establishing a fundamental security scanning process utilizing GitHub, GitHub Actions, and diverse security tools is a crucial undertaking. This initiative will provide valuable comprehension of code quality and security, enabling you to address potential risks and uphold a secure software environment. Armed with knowledge about the advantages, challenges, and recommended approaches, you can make informed choices regarding dealing with software containing identified bugs and determining their significance within your organization. Take the proactive step of setting up your scanning workflow today to safeguard your open source software effectively.
1. If you want to learn more around this as well as other issues plaguing supply chain security attend our course
2. If you or your friends need help around implementation of such setup. Contact Us
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
1 August 2026 – 2 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
3 August 2026 – 4 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
### [Mastering Third-Party Risk Management : Vendor & Software Supply Chain BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
Date: 4 August 2026Las Vegas, USA[](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
---
## Pages
### AI: Usage and Security
Date: 2026-03-21
URL: https://cyfinoid.com/research/ai-usage-and-security/
AI is quickly becoming part of how software is written, how teams search for information, how workflows get automated, and how decisions are supported. That makes AI both a productivity layer and a security layer. Cyfinoid’s AI research focuses on both sides at once: how organizations can use AI effectively, and how AI-enabled systems can introduce new trust, privacy, and security failures.
We are especially interested in the messy, real-world edge cases that appear when LLMs, copilots, agents, browser automation, internal knowledge, and external tools start getting connected together. Prompt injection, over-trusted agents, unsafe tool use, data leakage, weak review loops, and invisible automation boundaries all become part of the security problem.
This is an active and growing research area for us. Public material here will continue to expand as we turn experiments, notes, prototypes, and field observations into sharper tools, writeups, and training content.
## What We Study
- Secure adoption of LLMs, copilots, and AI-assisted workflows
- Prompt injection, context poisoning, and tool-use abuse
- Agent security, orchestration boundaries, and over-permissioned automation
- Data leakage, privacy, and knowledge-boundary failures in AI systems
- Practical ways to use AI for analysis without removing human judgment
- Evaluation methods for determining whether AI workflows are actually safe and useful
## Why This Matters
Many teams are adopting AI faster than they are defining trust boundaries around it. A model may not need to be “compromised” in the traditional sense for serious damage to happen. It may simply be connected to the wrong data, granted the wrong actions, or placed in a workflow that assumes too much.
We want to help organizations move beyond hype and fear. The real challenge is learning where AI genuinely improves outcomes, where it creates new attack surface, and what controls are needed if it is going to be trusted in development, operations, and security workflows.
## Current Direction
- Research on AI-enabled workflow risk in engineering and security operations
- Practical guidance for safer use of LLMs and agents inside real teams
- Experiments that explore human-AI and multi-agent interaction models
- Security-oriented thinking around browser-based and privacy-conscious AI tooling
## Early Public Signals
- Council of AI Bots: an exploratory experiment in multi-agent interaction and structured AI reasoning
- Ongoing work toward more practical public material around AI usage, agent behavior, and security implications
## Who This Research Helps
- Security teams evaluating AI adoption inside their organizations
- Engineering teams integrating AI into developer workflows
- Leaders trying to separate meaningful AI capability from risky automation theater
- Researchers interested in the overlap between AI usage, trust, and security
If your team is trying to use AI without creating blind trust, hidden data exposure, or unsafe automation, this is one of Cyfinoid’s active research directions.
## Community Contributions
- Council of AI bots
A.I.
## Blogs
[ ](https://cyfinoid.com/sbomplay-v0-0-7/)
[ ](https://cyfinoid.com/gh-navigator-released-full-coverage-of-githubs-data-and-control-planes/)
[ ](https://cyfinoid.com/decouple-and-conquer-understanding-control-and-data-planes-across-technology/)
[ ](https://cyfinoid.com/automating-a-known-weakness-introducing-keychecker/)
[ ](https://cyfinoid.com/introducing-3p-tracer-third-party-mapping-in-your-browser/)
[ ](https://cyfinoid.com/introducing-sbom-play-a-privacy-first-sbom-explorer-with-vulnerability-license-insights/)
---
### Internship @ Cyfinoid
Date: 2025-09-10
URL: https://cyfinoid.com/internship/
Cyber security domain always talks about lack of skilled resources. We decided not to whine but rather help with the cause.
At Cyfinoid, our interns don’t just shadow projects – they build. We offer **paid internships** where students are given real challenges that map to active research or training needs. With mentorship, they design, implement, and release complete tools. Many of these end up as open-source contributions used by the community.
### **What makes our internships different**
- Hands-on from day one → interns take ownership of real projects.
- Paid, not unpaid labor → we value their time and contribution.
- Mentorship, not micromanagement → guidance is given, but the work is theirs.
- Open-source output → successful projects are released publicly with interns’ names credited.
Some of the tools made by our Interns
- Fediverse Monitoring
Fediverse, Intern-project
- APK Analysis Automation
Android, Intern-project
- CFYVuln-Android
Android, Intern-project
Fediverse Monitoring
**Internship Project**
**Author: [Vansh Bulani](https://www.linkedin.com/in/vanshbulani/)**
The Fediverse is a collection of interconnected yet independent social networks that can communicate seamlessly using open protocols. Users on one platform can follow, interact with, and receive updates from users on entirely different platforms – all while staying within their preferred service. Most Fediverse platforms are free and open-source, fostering transparency and community-driven development.
Thanks to these open protocols, a wealth of data is publicly accessible through the right APIs. This project leverages that openness to collect and analyze various statistics across the Fediverse, providing deeper insights into its scale, activity, and growth.
**Project Link: [https://github.com/cyfinoid/fediverse-monitoring](https://github.com/cyfinoid/fediverse-monitoring)**
Categories :
Fediverse, Intern-project
APK Analysis Automation
**Internship Project**
**Author: [Vansh Bulani](https://www.linkedin.com/in/vanshbulani/)**
This Android APK analysis tool is a fast, modular, and extensible platform designed to bridge the long-standing gap between speed and depth in mobile application security analysis. Unlike traditional tools like Pithus that often suffer from high processing times and rigid workflows, our solution allows users to selectively run open-source tools in parallel, significantly reducing analysis time. Built on a containerized architecture, each analysis component runs independently in Docker, enabling seamless scalability and CI/CD integration. Results are unified and indexed using ElasticSearch, allowing for rapid, structured querying across diverse tool outputs. The platform is purpose-built for developers, researchers, and security professionals who need actionable insights – fast.
**Blog Post (ext): [Not Your Average APK Analyzer – How I Built a Tool for Deep Insights](https://github.com/vansh106/portfolio/blob/main/blogs/_posts/2024-04-05-Not-Your-Average-APK-Analyzer%EA%9E%89-How-I-Built-a-Tool-for-Deep-Insights.md)**
**Project Link: [https://github.com/cyfinoid/apk-analysis-automation](https://github.com/cyfinoid/apk-analysis-automation)**
Categories :
Android, Intern-project
CFYVuln-Android
**Internship Project **
**Author: [Johnny Antony Puthur](https://www.linkedin.com/in/johnnyantony/)**
This project contains an intentionally Vulnerable Android Application. This project serves as a valuable resource for individuals seeking to enhance their understanding of mobile application security. By providing a hands-on environment to explore and comprehend various vulnerabilities, this project facilitates practical learning in an interactive manner.
Participants can leverage this platform to identify common security weaknesses, develop effective mitigation strategies, and ultimately contribute to the advancement of secure mobile application development practices. Through deliberate exposure to vulnerabilities, individuals can refine their skills, stay abreast of emerging threats, and play a pivotal role in fortifying the mobile application landscape.
**Project Link: [https://github.com/cyfinoid/CFYVuln-android](https://github.com/cyfinoid/CFYVuln-android)**
Categories :
Android, Intern-project
### **Why this matters**
We believe the best way to fix the “skills gap” is to give people a real chance to build. Every intern who contributes here has tangible proof of what they’ve achieved, and the community benefits from fresh, working tools.
### How to Join Internship
We offer opportunities for Internship from time to time. Keep an eye on our [Public Social Media pages @ Linkedin](https://linkedin.com/company/cyfinoid) for announcements
Want to see all Cyfinoid’s open-source projects (intern-built + team-built)? [Visit our Open Source Hub →](/opensource-by-cyfinoid)
---
### Cloud Security
Date: 2025-06-29
URL: https://cyfinoid.com/research/cloud-security/
Cloud security is no longer about reviewing one provider at a time. Real environments span identities, APIs, managed services, third-party integrations, CI/CD, Kubernetes, serverless functions, storage layers, and provider-specific features that often get trusted more than they should. Cyfinoid’s cloud research focuses on how attackers actually discover and abuse those trust boundaries.
We are especially interested in multi-cloud and cloud-native environments where small mistakes can chain together: a weak identity assumption, an exposed service, an over-permissioned workload, a metadata path, an automation hook, or an unsafe integration that creates leverage far beyond its original scope.
Our goal is to help teams think about the cloud the way attackers do: through control planes, data planes, workload trust, service relationships, and the hidden assumptions that connect one system to another.
## What We Study
- Multi-cloud attack paths and trust boundaries across providers
- IAM abuse, privilege escalation, and identity-driven compromise
- Metadata exposure, workload pivots, and service-to-service trust
- Storage, secrets, and API exposure in cloud-native environments
- Kubernetes, serverless, and automation-related attack surface
- Third-party dependencies and Internet-facing cloud recon
## Why This Matters
Most defenders still organize cloud reviews around provider menus and service lists. Attackers do not. They look for repeatable building blocks: exposed assets, weak identity assumptions, dangerous defaults, automation mistakes, and relationships that can be chained into broader compromise.
That is why our cloud research emphasizes methodology over memorization. We want to understand which attack paths are provider-specific, which ones transfer across ecosystems, and where defenders should focus if they want to catch attacker thinking earlier.
### Community Contributions
- 3P Tracer
Cloud, Software Supply Chain Security
## How This Research Gets Used
- Building practical recon and visibility tooling
- Improving attacker-informed cloud reviews and assessments
- Turning recurring findings into trainings, labs, and defensive guidance
- Helping teams understand where cloud architecture, automation, and supply chain risk overlap
## Who This Research Helps
- Security teams reviewing modern cloud environments
- Red teamers and pentesters studying cloud abuse paths
- Platform teams responsible for identity, orchestration, and automation
- Engineering leaders who need a clearer model of cloud trust and exposure
If your team wants an attacker-informed view of modern cloud risk, this research also feeds directly into our cloud-focused trainings and private engagements.
### Recent Blogs
####
[Introducing 3P-Tracer: third-party mapping in your browser](https://cyfinoid.com/introducing-3p-tracer-third-party-mapping-in-your-browser/)
29th July 2025
No Comments
[ ](https://cyfinoid.com/introducing-3p-tracer-third-party-mapping-in-your-browser/)
[](https://cyfinoid.com/introducing-3p-tracer-third-party-mapping-in-your-browser/)
### Upcoming Trainings
### [Attacking Cloud Environments (AWS, Azure, GCP, DigitalOcean and Aliyun) BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-51037)
1 August 2026 – 2 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-51037)
### [Attacking Cloud Environments (AWS, Azure, GCP, DigitalOcean and Aliyun) BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-510371770400827)
3 August 2026 – 4 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-510371770400827)
### Previous Training Sessions
### [0wning the Cloud – AWS, Azure, GCP, DigitalOcean and Aliyun BlackHat EU 2025](https://www.blackhat.com/eu-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-46968)
8 December 2025 – 9 December 2025London, UK[](https://www.blackhat.com/eu-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-46968)
### [0wning the Cloud – AWS, Azure, GCP, DigitalOcean and Aliyun BlackHat USA 2025](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-445131736885703)
4 August 2025 – 5 August 2025Las Vegas, USA[](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-445131736885703)
### [0wning the Cloud – AWS, Azure, GCP, DigitalOcean and Aliyun BlackHat USA 2025](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-44513)
2 August 2025 – 3 August 2025Las Vegas, USA[](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-44513)
### [Going beyond shells! – hacking aws, google cloud, digitalocean and aliyun BlackHat USA 2024](https://www.blackhat.com/us-24/training/schedule/index.html#going-beyond-shells---hacking-aws-google-cloud-digitalocean-and-aliyun-virtual-374681706229570)
5 August 2024 – 6 August 2024Virtual[](https://www.blackhat.com/us-24/training/schedule/index.html#going-beyond-shells---hacking-aws-google-cloud-digitalocean-and-aliyun-virtual-374681706229570)
### [Going beyond shells! – hacking aws, google cloud, digitalocean and aliyun BlackHat USA 2024](https://www.blackhat.com/us-24/training/schedule/index.html#going-beyond-shells---hacking-aws-google-cloud-digitalocean-and-aliyun-virtual-37468)
3 August 2024 – 4 August 2024Virtual[](https://www.blackhat.com/us-24/training/schedule/index.html#going-beyond-shells---hacking-aws-google-cloud-digitalocean-and-aliyun-virtual-37468)
---
### Software Supply Chain Security
Date: 2025-06-29
URL: https://cyfinoid.com/research/software-supply-chain-security/
Software supply chain security is bigger than SBOMs and package dependencies. It includes the producer writing first-party code, the consumer combining libraries and services into new software, and the end user who installs, deploys, or depends on the finished product. It also includes the systems that shape trust along the way: developer desktops, repositories, CI/CD pipelines, SAST tooling, package ecosystems, artifacts, deployment tooling, containers, and cloud environments.
Cyfinoid’s research in this area focuses on how software trust breaks in practice. We study the places where convenience, automation, weak governance, and implicit trust intersect, and where attackers can turn that into repository access, dependency abuse, artifact tampering, release compromise, or broader organizational impact.
Our goal is to help teams understand software supply chain security as a full lifecycle problem rather than a compliance checkbox. That means looking beyond inventories and scans to the actual workflows, credentials, controls, and trust relationships that determine whether software can be trusted.
This also means our research naturally extends into adjacent areas such as CI/CD pipeline abuse and hardening, static analysis and SAST tooling, and desktop security for the systems where software is authored and trusted.
## What We Study
- Developer workstation, desktop, and identity-related supply chain risk
- Repository access, token exposure, and source control trust
- CI/CD abuse, pipeline security, build integrity, and release automation compromise
- Static analysis, SAST tooling, and where security tooling itself can create blind spots or misplaced trust
- Malicious dependencies, package ecosystem attacks, and third-party risk
- Inventory, SBOM, provenance, and trust verification beyond checkbox compliance
- Deployment, cloud, and runtime considerations that shape end-user trust
## Why This Matters
Attackers increasingly target the systems around the code rather than the code alone. A stolen developer key, an over-permissioned token, an unsafe workflow, or a compromised dependency can have far more impact than a single application bug.
Defenders need a broader model. Producers need to secure how software is authored and shipped. Consumers need to understand what external components and services are being pulled into their products. End users need better signals to judge what software they can trust. Our research is built around that full picture.
### Community Contributions
- GHNavigator: Repository Browser & Token Analyzer
Software Supply Chain Security
- keychecker : SSH Key analysis tool
Software Supply Chain Security
- 3P Tracer
Cloud, Software Supply Chain Security
- SBOM Play
Software Supply Chain Security
## How This Research Gets Used
- Building tools that make supply chain visibility and review easier
- Turning recurring attack paths into practical training, labs, and case studies
- Helping teams move from dependency-only thinking to lifecycle-wide trust analysis
- Translating offensive lessons into better governance, hardening, and detection decisions
## Who This Research Helps
- Developers and platform teams building first-party software
- Security teams reviewing repositories, pipelines, and release processes
- Organizations consuming third-party software, packages, and SaaS components
- Leaders who need clearer language for software trust, provenance, and operational risk
This research directly informs Cyfinoid’s software supply chain and CI/CD trainings, as well as our broader work on cloud and software trust.
### Upcoming Trainings
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
1 August 2026 – 2 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
3 August 2026 – 4 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
### [Mastering Third-Party Risk Management : Vendor & Software Supply Chain BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
Date: 4 August 2026Las Vegas, USA[](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
### Blogs
####
[SBOMPlay v0.0.7](https://cyfinoid.com/sbomplay-v0-0-7/)
31st December 2025
No Comments
[ ](https://cyfinoid.com/sbomplay-v0-0-7/)
[](https://cyfinoid.com/sbomplay-v0-0-7/)
####
[GH Navigator Released: Full Coverage of GitHub’s Data and Control Planes](https://cyfinoid.com/gh-navigator-released-full-coverage-of-githubs-data-and-control-planes/)
23rd September 2025
No Comments
[ ](https://cyfinoid.com/gh-navigator-released-full-coverage-of-githubs-data-and-control-planes/)
[](https://cyfinoid.com/gh-navigator-released-full-coverage-of-githubs-data-and-control-planes/)
####
[Automating a Known Weakness: Introducing keychecker](https://cyfinoid.com/automating-a-known-weakness-introducing-keychecker/)
22nd August 2025
No Comments
[ ](https://cyfinoid.com/automating-a-known-weakness-introducing-keychecker/)
[](https://cyfinoid.com/automating-a-known-weakness-introducing-keychecker/)
####
[Introducing 3P-Tracer: third-party mapping in your browser](https://cyfinoid.com/introducing-3p-tracer-third-party-mapping-in-your-browser/)
29th July 2025
No Comments
[ ](https://cyfinoid.com/introducing-3p-tracer-third-party-mapping-in-your-browser/)
[](https://cyfinoid.com/introducing-3p-tracer-third-party-mapping-in-your-browser/)
####
[Introducing SBOM Play: A Privacy-First SBOM Explorer with Vulnerability & License Insights](https://cyfinoid.com/introducing-sbom-play-a-privacy-first-sbom-explorer-with-vulnerability-license-insights/)
17th July 2025
No Comments
[ ](https://cyfinoid.com/introducing-sbom-play-a-privacy-first-sbom-explorer-with-vulnerability-license-insights/)
[](https://cyfinoid.com/introducing-sbom-play-a-privacy-first-sbom-explorer-with-vulnerability-license-insights/)
####
[Enhancing Open Source Security for Startups with Automated Scanning](https://cyfinoid.com/enhancing-open-source-security-for-startups-with-automated-scanning/)
19th September 2023
No Comments
[ ](https://cyfinoid.com/enhancing-open-source-security-for-startups-with-automated-scanning/)
[](https://cyfinoid.com/enhancing-open-source-security-for-startups-with-automated-scanning/)
### Previous Training Sessions
### [Attack and Defend Software Supply Chain DEFCON Trainings 2025](https://training.defcon.org/collections/def-con-training-las-vegas-2025/products/attack-and-defend-software-supply-chain-las-vegas-2025)
11 August 2025 – 12 August 2025Las Vegas, USA[](https://training.defcon.org/collections/def-con-training-las-vegas-2025/products/attack-and-defend-software-supply-chain-las-vegas-2025)
### [Attacking CI/CD Environments BruCON Trainings](https://www.brucon.org/training-details/attacking-cicd)
24 April 2025 – 25 April 2025Online[](https://cyfinoid.com/event/pipeline-predators-attacking-ci-cd-environments-brucon-trainings/)
### [Attack & Defend Software Supply Chain BlackHat Asia 2025](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-software-supply-chain-online--43054)
1 April 2025 – 2 April 2025Online[](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-software-supply-chain-online--43054)
### [Attack & Defend Software Supply Chains Nullcon 2025](https://nullcon.net/goa-2025/training/attack-and-defend-software-supply-chains)
3 March 2025 – 5 March 2025Goa, India[](https://cyfinoid.com/event/attack-defend-software-supply-chains-nullcon-2025/)
### [Attacking CI CD Environments Nullcon Hyderabad 24](https://nullcon.net/hyderabad-2024/training/attacking-ci-cd-environments)
2 May 2024 – 4 May 2024Hyderabad, India[](https://nullcon.net/hyderabad-2024/training/attacking-ci-cd-environments)
### [Attack & Defend Software Supply Chain BlackHat Asia](https://www.blackhat.com/asia-24/training/schedule/index.html#attack-and-defend-software-supply-chain-virtual-36009)
16 April 2024 – 17 April 2024Online[](https://www.blackhat.com/asia-24/training/schedule/index.html#attack-and-defend-software-supply-chain-virtual-36009)
### [Beyond the Code : Securing your software supply chain c0c0n 2023](https://india.c0c0n.org/2023/beyond-the-code-securing-your-software-supply-chain)
4 October 2023 – 5 October 2023Kochi, India[](https://india.c0c0n.org/2023/beyond-the-code-securing-your-software-supply-chain)
---
### Cyfinoid Research – Main
Date: 2025-06-26
URL: https://cyfinoid.com/
## Cybersecurity Research & Training Company
Cyfinoid Research conducts cutting-edge cybersecurity research and turns our findings into hands-on training. Our mission is to spark curiosity, share knowledge, and help others make meaningful contributions to the field.
Research Featured At **BlackHat, DEFCON, Nullcon, c0c0n, and other major conferences. **
[Check Upcoming Trainings](https://cyfinoid.com/trainings/)
*







#### **Trusted by 1000+ companies for Security Training & Research.**
From startups to Fortune 500s.
### Security Research Areas
Focused, original, and deeply technical — our research is designed to challenge assumptions and push boundaries.
#### Software Supply Chain
Cyfinoid researches software trust across the full delivery lifecycle, from the developer desktop and source repository to CI/CD, artifacts, deployment systems, and cloud environments. The focus is on understanding how modern software is attacked in practice and how producers, consumers, and end users can make better trust decisions.
[Read More](https://cyfinoid.com/software-supply-chain-security/)
#### Cloud Environments
Cyfinoid studies how attackers abuse identity, storage, metadata, automation, orchestration, and service-to-service trust in modern cloud environments. The goal is to help teams recognize the attack patterns that repeat across providers instead of relying only on vendor-specific checklists.
[Read More](https://cyfinoid.com/cloud-security/)
#### AI Usage & Security
Cyfinoid researches how AI is being adopted in real workflows and where that creates new security, privacy, and trust problems. This includes both helping teams use AI more effectively and understanding risks such as prompt injection, unsafe tool use, data leakage, and over-trusted automation.
[Read More](https://cyfinoid.com/research/ai-usage-and-security/)
### Security Trainings
Our trainings are driven by ongoing research. As our findings evolve, so do the curriculum — ensuring fresh, relevant, and practical content.
##### Upcoming Trainings
### [Attacking Cloud Environments (AWS, Azure, GCP, DigitalOcean and Aliyun) BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-51037)
1 August 2026 – 2 August 2026
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
1 August 2026 – 2 August 2026
### [Attacking Cloud Environments (AWS, Azure, GCP, DigitalOcean and Aliyun) BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-510371770400827)
3 August 2026 – 4 August 2026
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
3 August 2026 – 4 August 2026
### [Mastering Third-Party Risk Management : Vendor & Software Supply Chain BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
Date: 4 August 2026Las Vegas, USA
##
Trusted by our
customers & partners












- Hacking Multi-Cloud Infrastructure
- Attack & Defend Software Supply Chain
- Attacking CI/CD Pipelines
#### Hacking Multi-Cloud Infrastructure
Cloud providers may use different names, dashboards, and defaults, but attackers keep finding the same weak assumptions underneath. Hacking Multi-Cloud Infrastructure is designed to help participants think about the cloud the way attackers do: through identity, storage, metadata, orchestration, automation, trust boundaries, and the control-plane decisions that quietly shape real risk.
Instead of teaching a checklist for a single vendor, the training focuses on the patterns that transfer across environments. Participants learn how exposed assets are discovered, how identity assumptions get abused, how workloads and services can be pivoted through, and how cloud-native features such as Kubernetes, serverless, and automation expand the attack surface in ways many teams underestimate.
Depending on the delivery, the material may draw from AWS, Azure, Google Cloud, DigitalOcean, Alibaba Cloud, Kubernetes platforms, and adjacent cloud-native ecosystems. The exact service coverage changes from run to run, but the attacker methodology remains the core value: understanding which cloud attack paths are provider-specific, which ones repeat across providers, and how to adapt quickly instead of memorizing screens.
**Key topics include:**
- Enumerating cloud assets (S3 buckets, IAM roles, Spaces, OSS) without credentials
- Abusing SSRF and IMDSv2 for privilege escalation
- IAM exploitation on AWS, GCP, and Alibaba Cloud
- Escaping GKE clusters and impersonating service accounts on Google Cloud
- Attacking DigitalOcean Spaces and ECS instances
- Exploiting triggers and misconfigurations in AWS Lambda and lesser-known services
- Multi-cloud pivoting and lateral movement using native APIs
- Real-world breach simulations and pentest-inspired cloud lab scenarios
Students will gain repeatable methodologies, guided labs, and post-training resources to practice cloud offensive techniques in a safe environment.
This makes the training especially valuable for red teamers, pentesters, cloud security engineers, incident responders, and platform teams that want an attacker-informed view of cloud risk. It is built for people who want sharper thinking, practical attack-path understanding, and cloud security lessons they can carry from one environment to another.
[Detailed Outline & Upcoming Training ](#)
#### Attack & Defend Software Supply Chain
Software supply chain security is bigger than SBOMs, dependency lists, and compliance checkboxes. Attack & Defend Software Supply Chain is built around the full trust path that modern software depends on: the developer desktop, source repositories, CI/CD pipelines, package ecosystems, artifacts, deployment systems, containers, and the cloud environments where software finally runs.
The training also reflects the fact that software supply chain risk looks different depending on who you are. A producer writing first-party code has one set of responsibilities. A consumer taking libraries, platforms, and external services into a product has another. An end user deploying or relying on the finished software faces a different trust problem again. This course helps participants understand those perspectives together rather than treating supply chain security as a dependency-only problem.
Public conference deliveries are typically attack-led and focus heavily on how supply chain compromise happens in practice: malicious dependencies, repository abuse, CI/CD attacks, artifact trust failures, cloud-linked pivots, and the weak assumptions attackers exploit. Private and corporate deliveries can go deeper into defense, governance, hardening, provenance, and practical measures teams can use to reduce risk across their own software delivery lifecycle.
The result is a 360-degree view of software trust from code creation to cloud deployment. This training is ideal for developers, platform teams, DevOps practitioners, application security teams, and leaders who want to understand not just where supply chain risk exists, but how it actually turns into compromise and what a stronger defense model looks like in practice.
**Key topics include:**
- Attacking VS Code, IDE/browser extensions, Git misconfigurations, CI/CD, and package ecosystems
- Creating malicious dependencies and exploiting deployment systems (e.g., GitHub Actions, ArgoCD)
- Cloud & Kubernetes attack paths: IAM abuse, misconfigured images, insecure defaults
- Defense strategies based on SLSA, NIST SSDF, and governance-first models
- Generating and managing SBOMs, securing provenance, cloud audits, and runtime protection
- Role-based responsibilities, breach response, and infrastructure setup for red/blue team practice
Each module includes hands-on labs, real-world attack simulations, and post-training resources to continue your learning journey.
[Detailed Outline & Upcoming Training](#)
#### Attacking CI/CD Pipelines
CI/CD systems are no longer just build automation. They are high-trust control planes that connect source code, secrets, runners, artifacts, cloud permissions, and deployment paths. Attacking CI/CD Environments is built around that reality, showing participants how attackers see pipelines not as internal plumbing, but as some of the most valuable infrastructure in the modern software delivery stack.
The training focuses on how real attack paths emerge across repositories, workflow triggers, runners, agents, tokens, logs, caches, artifacts, webhooks, and external integrations. Participants learn how insecure defaults, workflow design mistakes, over-permissioned automation, and poorly isolated runners can create leverage for code tampering, secret theft, persistence, cloud abuse, and broader supply chain compromise.
Rather than centering on one platform alone, the course explores patterns that appear across GitHub Actions, GitLab CI, Jenkins, Bitbucket Pipelines, self-hosted runner environments, and related delivery workflows. It is attack-led by design, but it also helps participants think more clearly about misconfiguration audits, defensive review priorities, and the hardening decisions that matter most when pipelines are treated as critical trust infrastructure.
This makes the training especially relevant for DevOps engineers, build and platform teams, product security teams, application security professionals, and testers who need a realistic understanding of how modern delivery systems fail under attacker pressure. For organizations building and shipping software at speed, this course helps close the gap between “pipeline works” and “pipeline can actually be trusted.”
**Key topics include:**
- CI/CD fundamentals, architecture, and role in SDLC
- Common attack vectors and real-world CI/CD breaches
- Platform-specific attacks:
GitHub: Context injection, workflow tampering, secrets leakage, and malicious actions
- Jenkins: Script console abuse, plugin exploits, build artifact tampering
- GitLab CI: Runner exploitation, pipeline manipulation, insecure defaults
Cloud-native CI/CD misconfigurations and IAM flaws
Using CI/CD systems for persistence, stealth, and C2
Students gain hands-on experience through labs and a live CTF to reinforce exploitation techniques in realistic enterprise setups.
[Detailed Outline & Upcoming Training](#)
### TESTIMONIALS
What Students Say About Us
*
This wasn’t your typical cloud security class
This wasn’t your typical cloud security class - it was two full days of hands-on labs, real-world attack scenarios, and deep technical walkthroughs across AWS, Azure, GCP, DigitalOcean, and Aliyun. Each lab pushed us to think like attackers and defenders, and I walked away with a whole new appreciation for how exposed cloud environments can be if not properly secured.
… [ This wasn’t your typical cloud security classRead More »](https://cyfinoid.com/testimonial/this-wasnt-your-typical-cloud-security-class/)
**Darren Windham**
Principal - Forensic Services / Charles River Associates
**********
**
Smooth Learning Curve for Newcomers
*I'm a beginner level but was easy for me to understand all the topics because it was very clear the examples for each topic. Thanks for the help.*
**Attendee @ BlackHat USA**
**********
**
Valuable Insights for Real-World Mobile Pentesting
It was a very complete course providing me with very useful information that I will put in practice as I'm part of Mobile Pentest team in my organization, I'm very satisfied with the content and kudos to both instructors, they are pretty amazing with plenty of verifiable experience
**Attendee @ BlackHat USA**
**********
**
Hands-On Learning with Practical Cloud Insights
Learns a lot about Cloud structure and how we can get the leaking information and also how to use it. Well prepared tools and lab environment make us doing well. Really appreciate it.
**Attendee @ BlackHat**
**********
**
Enjoyable and Insightful Two-Day Workshop
Training Content, Discussions was on point. Really enjoyed two days session.
**Attendee @ c0c0n**
**********
**
Well-Executed Sessions with a Desire for More
The training was really good and trainers executed it in a fantastic way and they where very helpful. I really like to continue for 2 more days as the contents were interesting but time frame allocated was only 2 days.
**Attendee @ c0c0n**
**********
**
Knowledgeable Trainer and Practical Examples
Great knowledge and very helpful trainer and easy examples to relate with real world problems
**Attendee @ Nullcon**
**********
**
Deep dive training
"One of the most detailed training, it dives deep in the cloud hacking and explores real world attacks with case studies & thanks for the self-host vulnerable infra!"
**Attendee @ BlackHat USA**
**********
**
Insightful and Well-Worth the Investment
The presenters conveyed a significant amount of knowledge and I’m walking away with good value for $. Excellent work and great training!
**Attendee @ Blackhat USA**
**********
**
Impressive Content
Great delivery, very attentive, excellent knowledge base provided. The provision of material is a highlight.
**Attendee @ BlackHat USA**
**********
# Blogs
[ ](https://cyfinoid.com/sbomplay-v0-0-7/)
[ ](https://cyfinoid.com/gh-navigator-released-full-coverage-of-githubs-data-and-control-planes/)
[ ](https://cyfinoid.com/decouple-and-conquer-understanding-control-and-data-planes-across-technology/)
[ ](https://cyfinoid.com/automating-a-known-weakness-introducing-keychecker/)
[ ](https://cyfinoid.com/introducing-3p-tracer-third-party-mapping-in-your-browser/)
[ ](https://cyfinoid.com/introducing-sbom-play-a-privacy-first-sbom-explorer-with-vulnerability-license-insights/)
[Explore More](https://cyfinoid.com/blog/)
---
### Hacking Multi-Cloud Infrastructure
Date: 2024-06-19
URL: https://cyfinoid.com/trainings/hacking-multi-cloud-infrastructure/
Cloud providers may use different names, dashboards, and defaults, but attackers keep finding the same weak assumptions underneath. This hands-on training shows participants how to think about cloud the way attackers do: through identity, storage, metadata, orchestration, control planes, automation, and trust boundaries that repeat across environments.
The result is a practical methodology participants can carry from one cloud ecosystem to another instead of memorizing a single vendor checklist.
## What This Training Is
> This page gives a high-level overview of the training approach. Cyfinoid runs multiple cloud-focused courses, and the exact syllabus for a given run depends on the conference, audience, duration, and lab design for that event.
Depending on the delivery, the material may draw from AWS, Azure, Google Cloud, Alibaba Cloud, Linode, DigitalOcean, Vercel, Kubernetes platforms, and other adjacent cloud-native environments. We have experience across these ecosystems, but not every public run covers every provider or platform.
Across our cloud trainings, we cover more than 100 cloud services and platform components. Any specific run will focus on the subset that best fits that event’s syllabus, but the attacker methodology transfers across them.
For the exact modules, lab setup, student requirements, supported platforms, and account needs for a specific session, please check that conference or event page.
## Why It Matters
Most teams still review cloud risk provider by provider. Attackers do not. They look for exposed assets, weak identity assumptions, metadata abuse, workload pivots, over-permissioned services, and trust relationships that can be chained into larger compromise.
Clouds look different on the surface, but underneath they repeat the same attacker-relevant building blocks. Once you understand how attackers reason about those building blocks in one provider, you can often adapt that methodology to another. That is the core focus of this training: helping participants recognize the common patterns behind cloud compromise instead of memorizing vendor-specific screens.
## What Participants Will Learn
Participants will learn how to:
- Map Internet-facing cloud attack surface and identify useful entry points
- Think about identity, workload, storage, and control-plane trust boundaries the way attackers do
- Turn misconfigurations, weak assumptions, and application bugs into cloud leverage
- Recognize which attack paths are provider-specific and which ones transfer across providers
- Apply lessons from one cloud ecosystem to another with the right adjustments
- Use offensive understanding to improve reviews, detections, and defensive design
## What Makes This Training Different
- Methodology-first, not checklist-first
- Built to help participants transfer lessons from one provider to another
- Grounded in real pentest observations, cloud attack paths, and defensive review experience
- Flexible enough to support different conference formats, durations, and private team needs
- Designed to help both testers and defenders think more clearly about cloud risk
## Example Questions The Training Explores
1. How do attackers discover exposed cloud assets and services without credentials?
2. How do storage and identity misconfigurations create initial access, privilege escalation, or data theft opportunities?
3. How can metadata services, workload identities, and service-to-service trust be abused?
4. How do application-layer bugs such as SSRF become cloud control-plane problems?
5. What parts of a cloud attack chain stay consistent across providers, and where do provider-specific differences matter most?
6. How do Kubernetes, serverless, and automation features change the cloud attack surface?
7. How should defenders review cloud environments if they want to catch attacker thinking earlier?
8. How can teams test their assumptions before they turn into exploitable cross-cloud patterns?
## Who Should Attend
- Red teamers and pentesters
- Cloud security engineers and defenders
- Incident responders and detection engineers
- Platform teams that want an attacker-informed view of cloud risk
## Training Format
- Hands-on labs built around realistic attack paths
- Guided walkthroughs of offensive techniques and their defensive implications
- Scenarios inspired by real-world pentest findings and breach patterns
- A methodology-first approach that emphasizes patterns transferable across providers
- Exact provider coverage and lab mix adjusted to the specific conference or private delivery
## Student Requirements
- Familiarity with security testing basics such as common OWASP Top 10 issues
- Basic comfort with Linux command-line tools such as grep, cut, dig, nslookup, vim, and ssh
- Familiarity with at least one major cloud platform or cloud console is helpful
- High-level understanding of technologies such as Kubernetes and Terraform is useful, but not required
Exact prerequisites may vary by run. Always check the conference or event page for the authoritative student requirements.
## What Students Should Bring
- Laptop running Windows 10+, macOS, or Linux
- Updated browser such as Chrome or Firefox
- Reliable Internet connection
- Any cloud accounts or platform-specific setup required for labs, if requested for that run
Please use your own accounts when a specific run requires them. Shared accounts can interfere with lab progress and lead to inconsistent results.
## What Students Receive
- Detailed step-by-step lab manual for the exercises covered during the class
- Slide deck for the material covered during the training
- Access to Terraform scripts for environment setup after class
## Next Sessions
### [Attacking Cloud Environments (AWS, Azure, GCP, DigitalOcean and Aliyun) BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-51037)
1 August 2026 – 2 August 2026[*](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-51037)
### [Attacking Cloud Environments (AWS, Azure, GCP, DigitalOcean and Aliyun) BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-510371770400827)
3 August 2026 – 4 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-510371770400827)
## Testimonials
*
Deep dive training
"One of the most detailed training, it dives deep in the cloud hacking and explores real world attacks with case studies & thanks for the self-host vulnerable infra!"
**Attendee @ BlackHat USA**
**********
**
Hands-On Learning with Practical Cloud Insights
Learns a lot about Cloud structure and how we can get the leaking information and also how to use it. Well prepared tools and lab environment make us doing well. Really appreciate it.
**Attendee @ BlackHat**
**********
**
This wasn’t your typical cloud security class
This wasn’t your typical cloud security class - it was two full days of hands-on labs, real-world attack scenarios, and deep technical walkthroughs across AWS, Azure, GCP, DigitalOcean, and Aliyun. Each lab pushed us to think like attackers and defenders, and I walked away with a whole new appreciation for how exposed cloud environments can be if not properly secured.
… [ This wasn’t your typical cloud security classRead More »](https://cyfinoid.com/testimonial/this-wasnt-your-typical-cloud-security-class/)
**Darren Windham**
Principal - Forensic Services / Charles River Associates
**********
## Recent Previous Run of this class
### [0wning the Cloud – AWS, Azure, GCP, DigitalOcean and Aliyun BlackHat EU 2025](https://www.blackhat.com/eu-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-46968)
8 December 2025 – 9 December 2025London, UK[](https://www.blackhat.com/eu-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-46968)
### [0wning the Cloud – AWS, Azure, GCP, DigitalOcean and Aliyun BlackHat USA 2025](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-445131736885703)
4 August 2025 – 5 August 2025Las Vegas, USA[](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-445131736885703)
### [0wning the Cloud – AWS, Azure, GCP, DigitalOcean and Aliyun BlackHat USA 2025](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-44513)
2 August 2025 – 3 August 2025Las Vegas, USA[](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-44513)
### [Going beyond shells! – hacking aws, google cloud, digitalocean and aliyun BlackHat USA 2024](https://www.blackhat.com/us-24/training/schedule/index.html#going-beyond-shells---hacking-aws-google-cloud-digitalocean-and-aliyun-virtual-374681706229570)
5 August 2024 – 6 August 2024Virtual[](https://www.blackhat.com/us-24/training/schedule/index.html#going-beyond-shells---hacking-aws-google-cloud-digitalocean-and-aliyun-virtual-374681706229570)
### [Going beyond shells! – hacking aws, google cloud, digitalocean and aliyun BlackHat USA 2024](https://www.blackhat.com/us-24/training/schedule/index.html#going-beyond-shells---hacking-aws-google-cloud-digitalocean-and-aliyun-virtual-37468)
3 August 2024 – 4 August 2024Virtual[](https://www.blackhat.com/us-24/training/schedule/index.html#going-beyond-shells---hacking-aws-google-cloud-digitalocean-and-aliyun-virtual-37468)
## How to attend
Cyfinoid offers its trainings via multiple international conference such as BlackHat USA and others.
[Contact Us for Private / Corporate Session](https://cyfinoid.com/contact/)
---
### Open Source by Cyfinoid
Date: 2024-04-10
URL: https://cyfinoid.com/opensource-by-cyfinoid/
Cyber security domain always talks about lack of skilled resources and tooling. We decided not to whine but rather help with the cause.
At Cyfinoid, open source is how we put this into action. Some projects are developed by our research team, while others come directly from our interns, who build complete tools during their paid internships.
This page is the central hub for all our open-source work. Each project is clearly attributed, so credit goes where it belongs.
- All
- A.I.
- Android
- Cloud
- Fediverse
- Intern-project
- Software Supply Chain Security
- GHNavigator: Repository Browser & Token Analyzer
Software Supply Chain Security
- keychecker : SSH Key analysis tool
Software Supply Chain Security
- Fediverse OSINT
Fediverse
- 3P Tracer
Cloud, Software Supply Chain Security
- SBOM Play
Software Supply Chain Security
- Fediverse Monitoring
Fediverse, Intern-project
- Council of AI bots
A.I.
- APK Analysis Automation
Android, Intern-project
- CFYVuln-Android
Android, Intern-project
Want to know how our interns build and release tools? → [Read about our Internship Program ](https://cyfinoid.com/internship/)
---
### Attacking CI/CD Environments
Date: 2024-03-09
URL: https://cyfinoid.com/trainings/attacking-ci-cd-environments/
CI/CD systems are no longer just build automation. They are high-trust control planes that connect source code, secrets, runners, artifacts, cloud permissions, and deployment paths. This hands-on training shows participants how attackers think about CI/CD: as a privileged automation layer that can be abused for initial access, code tampering, secret theft, persistence, and pivots into broader software delivery environments.
The goal is not to memorize one vendor’s interface. Participants learn how to reason about repositories, workflow triggers, runners, agents, build scripts, artifacts, logs, webhooks, and integrations across both self-hosted and SaaS-based environments.
Cyfinoid approaches this area as part of the broader [software supply chain security](https://cyfinoid.com/research/software-supply-chain-security/) problem. That means this training focuses on how trust breaks between developers, source control, automation platforms, cloud services, and deployment systems rather than treating CI/CD as an isolated build feature.
## What This Training Is
This page gives a high-level overview of the training approach. Cyfinoid runs multiple software delivery and cloud-focused courses, and the exact syllabus for a given run depends on the conference, audience, duration, and lab design for that event.
Depending on the delivery, the material may draw from GitHub Actions, GitLab CI, Jenkins, Bitbucket Pipelines, Gitea, self-hosted runners, cloud-native delivery workflows, artifact handling, and surrounding identity or integration layers. We have experience across both self-hosted and SaaS-based CI/CD environments, but not every public run covers every platform.
This training is attack-led, with practical attention to misconfiguration audits and defensive implications. The core emphasis is on how CI/CD systems are abused in practice, how insecure pipeline design creates leverage for attackers, and what teams should review if they want to harden their delivery workflows. For the exact platform coverage, lab design, student requirements, and account needs for a specific session, please check that conference or event page.
## Why It Matters
Many organizations still think of CI/CD as internal plumbing. Attackers see something different: a privileged automation layer with access to source code, tokens, secrets, artifacts, deployment rights, and sometimes direct cloud or production access.
CI/CD platforms may differ in syntax and features, but the same weak assumptions keep appearing: untrusted inputs in trusted workflows, over-permissioned tokens, poorly isolated runners, insecure defaults, unsafe artifact trust, and dangerous integrations. This training is built to help participants recognize those repeating patterns and understand how they turn into real compromise.
## What Participants Will Learn
Participants will learn how to:
- Understand why CI/CD systems are attractive attack surfaces in modern software delivery
- Map trust boundaries across repositories, workflows, runners, secrets, artifacts, and deployment steps
- Identify common CI/CD attack paths in both self-hosted and SaaS-based environments
- Abuse GitHub, GitLab, Jenkins, Bitbucket, and similar CI/CD primitives such as workflow manipulation, context injection, secret leakage, and runner misuse
- Audit pipeline design, insecure defaults, and common misconfigurations that create exploitable paths
- Explore how CI/CD weaknesses chain into artifact tampering, cloud abuse, and broader software supply chain compromise
- Use offensive understanding to improve audits, reviews, and platform hardening decisions
## What Makes This Training Different
- Focused on attacker methodology, not just platform administration
- Built to cover both self-hosted and SaaS CI/CD environments
- Treats pipelines as part of a wider software delivery control plane, not a standalone build tool
- Grounded in realistic abuse paths across repositories, runners, cloud integrations, and deployment workflows
- Flexible enough to adapt to different conference formats, durations, and private team needs
## Example Questions The Training Explores
1. How do attackers gain useful leverage in a CI/CD system without starting from full administrative control?
2. Which trust boundaries matter most in practice: repository write access, pull requests, runner control, artifacts, tokens, or cloud integrations?
3. How do insecure defaults and workflow design mistakes create exploitable paths in GitHub Actions, GitLab CI, Jenkins, Bitbucket Pipelines, and similar platforms?
4. How can secrets, logs, caches, webhooks, artifacts, and external actions become attack surfaces?
5. How do self-hosted runners and cloud-connected pipelines turn CI/CD issues into broader infrastructure compromise?
6. How can CI/CD systems be abused for persistence, stealth, command-and-control, or software tampering?
7. What should defenders audit first if they want to catch attacker thinking earlier in the delivery lifecycle?
## Who Should Attend
- Red teamers and pentesters
- DevOps engineers, platform teams, and build engineers
- Security engineers and product security teams
- Solution architects and developers responsible for CI/CD design or review
## Training Format
- Hands-on labs built around realistic CI/CD attack paths
- Guided walkthroughs of offensive techniques across repositories, runners, pipelines, and integrations
- Platform coverage adjusted to the specific conference or private delivery
- Offensive-first methodology with discussion of common misconfigurations, audit techniques, and defensive implications
- Some runs may include a capstone challenge or CTF-style exercise, depending on the format
## Student Requirements
- Basic familiarity with CI/CD and pipeline concepts
- Comfort with Git, browser-based tooling, and common developer workflows
- Familiarity with at least one source control or CI/CD platform is helpful, but not required
Exact prerequisites may vary by run. Always check the conference or event page for the authoritative student requirements.
## What Students Should Bring
- Laptop with a working browser and unrestricted Internet access
- Administrative access on the laptop in case troubleshooting is needed during labs
- Any required free accounts for GitHub, GitLab, Bitbucket, or similar platforms, if requested for that run
Some platforms place limits on newly created accounts. If a specific session requires accounts, create them in advance and follow the conference instructions. For hands-on sessions, older accounts may work better than freshly created ones.
## What Students Receive
- Detailed step-by-step lab manual for the exercises covered during the class
- Slide deck for the material covered during the training
- Cloud-based or virtual lab environment with the required tools pre-configured for the event
- Practical scenarios that participants can reuse for further testing and internal reviews
### Next Sessions
No events are found.
### Previous Run of this class
### [Attacking CI/CD Environments BruCON Trainings](https://www.brucon.org/training-details/attacking-cicd)
24 April 2025 – 25 April 2025Online[](https://cyfinoid.com/event/pipeline-predators-attacking-ci-cd-environments-brucon-trainings/)
### [Attacking CI CD Environments Nullcon Hyderabad 24](https://nullcon.net/hyderabad-2024/training/attacking-ci-cd-environments)
2 May 2024 – 4 May 2024Hyderabad, India[](https://nullcon.net/hyderabad-2024/training/attacking-ci-cd-environments)
### How to attend
Cyfinoid offers its trainings via multiple international conference such as BlackHat USA and others, We do offer private trainings also.
[Contact Us for Private / Corporate Session](https://cyfinoid.com/contact/)
---
### SBoM Masterclass
Date: 2024-03-09
URL: https://cyfinoid.com/trainings/sbom-masterclass/
### Overview
SBoM’s are one of the most focused entities in current secure development paradigm. However, focus is solely on creation of SBoM owing to its compliance requirements it’s been focused as another checkbox at this point. However, SBoM’s for the first time in a long run is trying to solve the right problem i.e. Inventory.
While we believe that SBoM on its own is not the final solution for supply chain security issues, we also strongly believe it’s a solid step in the right direction. Hence, we have come up with this SBoM Masterclass where we wanted to focus on not just creation but consumption and usage of SBoM. SBoM being the inventory has a myriad usage that goes beyond the limited scope of just thirdparty library vulnerability status detection. This course focuses on different usage and identifies scenarios where SBoM would be useful.
### WHO SHOULD ATTEND
- Software Developers and Engineers
- IT Managers
- Security Analysts
- DevOps Practitioners
- CTOs and Decision Makers in IT
### EXPECTED AUDIENCE LEVEL
Beginner / Intermediate
A!endees need to have a basic understand of software development life cycle. We will cover SBoM from start to finish but awareness of general development practices, git and GitHub usage is expected from them. Course assumes basic familiarity with command-line and Linux.
### WHAT STUDENTS WILL BE PROVIDED WITH
- Very Detailed step by step instruction manual for all challenges covered during the class.
- A Slide deck containing the slides covered during the class.
- A set of Cloud Virtual Machine with all required tools pre-configured.
### WHAT STUDENTS SHOULD BRING
Our labs are cloud based, and a browser should be sufficient. However, we will still suggest following hardware specs:
- Laptop with working browser & unrestricted internet access (at least port 80 and 443. However, some web-socket connections might be required.)
- We would still recommend bringing a laptop with full administrative access in case any troubleshooting is required.
A!endees will need to come with a GitHub account. A fresh organization would be created for all the operations. Any other associated tooling will be provided over a cloud VM for this activity.
### COURSE ABSTRACT
Supply chain security is an ever-present threat looming over organizations. Software Bill of Materials (SBOMs) are a critical piece of the puzzle, yet the process of creating, managing, and utilizing SBOMs is enveloped in mystery for many. This training demystifies the subject, offering hands-on expertise to practitioners caught during this challenge. This masterclass adopts a practical and focused approach, starting with an understanding of what SBOMs are, followed by the processes of creating, storing, and validating them. We then delve into how maintaining such an inventory can help organizations prioritize their security efforts from a supply chain perspective.
### COURSE SYLLABUS
#### Day 1
#### SBoM Basics
- Understanding Supply Chain Security
- Where does SBoM Fit into the Picture
- Basics of SBoM: Introduction to SBOM concepts, purposes, and benefits.
- Types of SBoM: Overview of different SBOM formats. (SPDX, SWID, CycloneDX)
#### Creation and Validation of SBoM
- How to Create SBoM
- How to Establish Provenance
- Where to Store Provenance
- How to Validate Provenance
- How to Create SBoM Automatically
- Full Cascading SBoM (all encompassing SBoM’s for multi level dependency tree)
#### How to Use SBoM
- SBoM for Dependency Upgrades for Projects: Managing and upgrading project dependencies.
- SBoM for Vulnerability Identification: Leveraging SBOM for vulnerability detection.
- Identifying Your Most Used Third-Party Dependencies across projects: Understanding dependency usage patterns.
- Dependency Map Across Projects: Visualizing dependencies and their relationships.
- Auditing Projects Using SBOM: Conducting project audits using SBOM data.
- License Validation via SBOMs: Ensuring licensing compliance.
#### Enhancing SBoM
- Isolate False Positives: Differentiating real threats and false positives.
- VDR and VEX Reports: Utilizing VDR and VEX in the SBOM context.
- Advanced Dependency Tracking: Deeper analysis of indirect dependencies.
- Automated Compliance Checks: Ensuring SBOM compliance with automation.
- SBOM Data Visualization: Visual tools for complex dependency analysis.
- Integrating SBOM with Incident Response Plans: Leveraging SBOM in cybersecurity incidents.
#### Beyond SBoM
- Cryptographic Bill of Material
- SaaS Bill of Material
- More xBoM’s and how to generate them
###
### Next Sessions
No events are found.
### Previous Run of this class
No events are found.
### How to attend
Cyfinoid offers its trainings via multiple international conference such as BlackHat USA and others, We do offer private trainings also.
[Contact Us for Private / Corporate Session](https://cyfinoid.com/contact/)
---
### Attack & Defend Software Supply Chain
Date: 2024-03-09
URL: https://cyfinoid.com/trainings/attack-defend-software-supply-chain/
Software supply chain security is bigger than SBOMs and package dependencies. It includes the producer writing first-party code, the consumer combining libraries and services into new software, and the end user who installs, operates, or depends on the finished product. It also includes the systems that shape trust along the way: developer desktops, IDEs, repositories, CI/CD, deployment tooling, container images, package ecosystems, and cloud environments.
Those perspectives matter because each persona inherits risk differently. A producer has to secure how software is authored and shipped. A consumer has to understand what external components, services, and build dependencies are being pulled into a product. An end user has to evaluate what software can be trusted, how it was built, and what signals are available when something goes wrong.
Cyfinoid specializes in this area. Our [software supply chain security research](https://cyfinoid.com/research/software-supply-chain-security/) reflects the same broader view behind this training program: supply chain security is not just about generating SBOMs or scanning dependencies, but about understanding how software is built, moved, trusted, attacked, and defended from the developer’s desktop to cloud deployment.
## What This Training Is
This page gives a high-level overview of the training program. Cyfinoid runs both attack-focused and defense-focused software supply chain classes. Public conference deliveries are primarily attack-led, while private / corporate engagements more often emphasize defending the software supply chain, improving internal controls, and helping teams operationalize the lessons.
The exact syllabus for a given run depends on the conference, audience, duration, and lab design for that event. If you plan to attend a public session, please review that conference page beforehand for the authoritative module list, labs, student requirements, and delivery specifics.
Across these courses, we aim to provide a 360-degree view of software supply chain security, from the developer’s desktop and repository workflows through CI/CD, deployment systems, containers, and cloud environments. The material is designed to give practical guidance to producers, consumers, and end users rather than treating software supply chain security as a dependency-only problem.
## Why It Matters
Software supply chain risk no longer starts and ends with open-source dependencies. Attackers look for trust boundaries they can abuse across first-party code, developer tooling, repositories, build systems, package ecosystems, release automation, and deployment platforms.
This training helps participants understand both sides of that problem: how supply chain attacks happen in practice, and how to build defenses that hold up in real delivery environments. The goal is not to teach a single checklist, but to help teams see how trust breaks across the full path from code creation to software consumption.
## What Participants Will Learn
Participants will learn how to:
- Understand software supply chain risk beyond SBOMs and third-party packages
- Analyze supply chain risk from the perspectives of producers, consumers, and end users
- Attack developer environments, VS Code workspaces, extensions, Git, and repository workflows
- Abuse CI/CD pipelines, custom runners, release processes, and deployment platforms
- Create and analyze malicious dependencies and package ecosystem attack paths
- Explore container, Kubernetes, cloud, and IAM-related supply chain exposure
- Translate frameworks such as SLSA and NIST SSDF into practical controls
- Improve inventory, SBOM generation, provenance, hardening, detection, and response
## How The Program Is Delivered
- Cyfinoid runs both attack and defense classes in this area
- Conference deliveries are primarily attack-focused and typically emphasize offensive labs, attacker methodology, and exploitation paths
- Private / corporate deliveries can be tailored toward defense, governance, hardening, and operational improvements for internal teams
- Hands-on labs, real-world case studies, and guided walkthroughs are adapted to the event format and audience
- Exact coverage varies by run, so attendees should always check the specific conference or event page beforehand
## Guidance For All Three Personas
- Producers: teams building and maintaining first-party code, internal tooling, and release pipelines
- Consumers: teams taking libraries, platforms, SaaS components, and third-party dependencies and turning them into new software
- End users: organizations that deploy, buy, or rely on finished software and need to evaluate its trustworthiness and exposure
## Topics Covered
- Introduction to software supply chain security
- Supply chain risk beyond code dependencies
- Exploiting VS Code workspaces
- Trojanizing IDE and browser extensions
- Exploiting Git and GitHub misconfigurations
- Attacking CI pipelines and custom runners
- Creating malicious dependencies
- Attacking package ecosystems such as npm and Gradle
- Exploiting deployment systems such as GitHub Actions and ArgoCD
- Leveraging container image misconfigurations
- Exploring cloud and Kubernetes attack paths
- Attacking cloud environments through IAM, data exposure, and configuration flaws
- Exploiting Kubernetes misconfigurations and insecure defaults
- Applying SLSA and NIST SSDF in practical settings
- Improving governance, inventory, SBOMs, provenance, and baseline controls
- Strengthening runtime security, detection, response, and recovery
## Who Should Attend
- Software producers such as developers, engineers, and platform teams
- Software consumers such as product teams, DevOps practitioners, and teams integrating third-party components into delivered software
- Software end users such as security teams, risk owners, IT managers, engineering managers, and leadership stakeholders
## Training Format
- Attack-led, defense-led, or blended delivery depending on the event
- Hands-on labs with intentionally vulnerable environments
- Real-world case studies and guided walkthroughs
- Practical takeaways that can be used across the path from developer desktop to cloud deployment
## Student Requirements
Basic knowledge of software development and IT security concepts is assumed. Familiarity with cloud platforms and CI/CD processes is helpful, but not mandatory.
Exact prerequisites may vary by run. Always check the conference or event page for the authoritative student requirements.
## What Students Should Bring
- Laptop with a working browser and unrestricted Internet access
- Administrative access on the laptop in case troubleshooting is needed during labs
Some labs may require access to common development or cloud services. Instructions will be provided before the class so students can prepare accounts in advance when needed.
## What Students Receive
- Detailed step-by-step lab manual for the challenges covered during class
- Slide deck for the material covered during the training
- Post-training capture-the-flag challenges for further practice
- Attack and defense infrastructure guide for self-practice
### Next Sessions
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
1 August 2026 – 2 August 2026[*](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
3 August 2026 – 4 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
### [Mastering Third-Party Risk Management : Vendor & Software Supply Chain BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
Date: 4 August 2026Las Vegas, USA[](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
## Testimonials
*
Knowledgeable Trainer and Practical Examples
Great knowledge and very helpful trainer and easy examples to relate with real world problems
**Attendee @ Nullcon**
**********
**
Well-Executed Sessions with a Desire for More
The training was really good and trainers executed it in a fantastic way and they where very helpful. I really like to continue for 2 more days as the contents were interesting but time frame allocated was only 2 days.
**Attendee @ c0c0n**
**********
**
Enjoyable and Insightful Two-Day Workshop
Training Content, Discussions was on point. Really enjoyed two days session.
**Attendee @ c0c0n**
**********
### Previous Run of this class
### [Attack and Defend Software Supply Chain DEFCON Trainings 2025](https://training.defcon.org/collections/def-con-training-las-vegas-2025/products/attack-and-defend-software-supply-chain-las-vegas-2025)
11 August 2025 – 12 August 2025Las Vegas, USA[](https://training.defcon.org/collections/def-con-training-las-vegas-2025/products/attack-and-defend-software-supply-chain-las-vegas-2025)
### [Attack & Defend Software Supply Chain BlackHat Asia 2025](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-software-supply-chain-online--43054)
1 April 2025 – 2 April 2025Online[](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-software-supply-chain-online--43054)
### [Attack & Defend Software Supply Chains Nullcon 2025](https://nullcon.net/goa-2025/training/attack-and-defend-software-supply-chains)
3 March 2025 – 5 March 2025Goa, India[](https://cyfinoid.com/event/attack-defend-software-supply-chains-nullcon-2025/)
### [Attack & Defend Software Supply Chain BlackHat Asia](https://www.blackhat.com/asia-24/training/schedule/index.html#attack-and-defend-software-supply-chain-virtual-36009)
16 April 2024 – 17 April 2024Online[](https://www.blackhat.com/asia-24/training/schedule/index.html#attack-and-defend-software-supply-chain-virtual-36009)
### How to attend
Cyfinoid offers its trainings via multiple international conference such as BlackHat USA and others, We do offer private trainings also.
[Contact Us for Private / Corporate Session](https://cyfinoid.com/contact/)
---
### Communication preferences
Date: 2023-10-27
URL: https://cyfinoid.com/communication-preferences/
[automatewoo_communication_preferences]
---
### Beyond the Code: Securing Your Software Supply Chain
Date: 2023-08-08
URL: https://cyfinoid.com/trainings/beyond-the-code-securing-your-software-supply-chain/
**[THIS COURSE IS NOW RETIRED AND IS SUPERSEEDED BY ATTACK AND DEFEND SOFTWARE SUPPLY CHAIN.](https://cyfinoid.com/trainings/attack-defend-software-supply-chain/)**
[Contact Us for Private / Corporate Session](https://cyfinoid.com/contact/)
---
### Terms and Conditions
Date: 2023-04-28
URL: https://cyfinoid.com/terms-and-conditions/
1. Introduction
Welcome to Cyfinoid Research! By using our website (located at [https://cyfinoid.com](https://cyfinoid.com/)) and our digital products, you agree to be bound by the following terms and conditions (“Terms and Conditions”) and our Privacy Policy (available at [https://cyfinoid.com/privacy-policy/](https://cyfinoid.com/privacy-policy/)). If you do not agree with these terms, you must discontinue using our website and services.
1. Registration and Account Security
To access certain features of our website, you may be required to create an account. When registering, you must provide accurate and complete information. You are solely responsible for maintaining the confidentiality of your account and password, and for any activities that occur under your account.
We reserve the right to suspend or terminate your account at our sole discretion if we suspect any unauthorized or fraudulent activity.
1. Intellectual Property Rights
All content on our website, including but not limited to text, images, graphics, logos, and digital downloads, is the property of Cyfinoid Research or its content suppliers and is protected by Indian and international copyright laws. Unauthorized use, reproduction, or distribution of any content is strictly prohibited.
1. Refund and Returns Policy
By purchasing our digital products, you agree to our Refund and Returns Policy, which can be found at [https://cyfinoid.com/refund_returns/](https://cyfinoid.com/refund_returns/). Please read this policy carefully before making a purchase.
1. User Conduct
As a user of our website, you agree not to:
a. Use our website or services for any illegal or unauthorized purpose. b. Post or transmit any content that is harmful, threatening, abusive, harassing, defamatory, or otherwise objectionable. c. Attempt to gain unauthorized access to our systems, servers, or user accounts. d. Intentionally or unintentionally violate any applicable local, state, national, or international law.
1. Termination
We reserve the right to terminate your access to our website and services without prior notice if you violate these Terms and Conditions or engage in any conduct that we, in our sole discretion, deem harmful or inappropriate.
1. Governing Law
These Terms and Conditions shall be governed by and construed in accordance with the laws of Madhya Pradesh, India. Any disputes arising in connection with these Terms and Conditions shall be subject to the exclusive jurisdiction of the courts of Madhya Pradesh, India.
1. Changes to Terms and Conditions
We reserve the right to update or modify these Terms and Conditions at any time without prior notice. Your continued use of our website and services constitutes your acceptance of any such changes. We encourage you to review these Terms and Conditions periodically.
1. Contact Information
If you have any questions or concerns regarding these Terms and Conditions, please contact us at [support@cyfinoid.com](mailto:support@cyfinoid.com).
By using the Cyfinoid Research website and services, you acknowledge that you have read, understood, and agreed to be bound by these Terms and Conditions.
---
### Privacy Policy
Date: 2023-04-28
URL: https://cyfinoid.com/privacy-policy/
## Who we are
We are Cyfinoid Research: a training and consulting firm focused on deep technical research.
## Comments
When visitors leave comments on the site we collect the data shown in the comments form, and also the visitor’s IP address and browser user agent string to help spam detection.
An anonymised string created from your email address (also called a hash) may be provided to the Gravatar service to see if you are using it. The Gravatar service Privacy Policy is available here: [https://automattic.com/privacy/](https://automattic.com/privacy/). After approval of your comment, your profile picture is visible to the public in the context of your comment.
## Media
** **If you upload images to the website, you should avoid uploading images with embedded location data (EXIF GPS) included. Visitors to the website can download and extract any location data from images on the website.
## Cookies
If you leave a comment on our site you may opt in to saving your name, email address and website in cookies. These are for your convenience so that you do not have to fill in your details again when you leave another comment. These cookies will last for one year.
If you visit our login page, we will set a temporary cookie to determine if your browser accepts cookies. This cookie contains no personal data and is discarded when you close your browser.
When you log in, we will also set up several cookies to save your login information and your screen display choices. Login cookies last for two days, and screen options cookies last for a year. If you select “Remember Me”, your login will persist for two weeks. If you log out of your account, the login cookies will be removed.
If you edit or publish an article, an additional cookie will be saved in your browser. This cookie includes no personal data and simply indicates the post ID of the article you just edited. It expires after 1 day.
## Embedded content from other websites
Articles on this site may include embedded content (e.g. videos, images, articles, etc.). Embedded content from other websites behaves in the exact same way as if the visitor has visited the other website.
These websites may collect data about you, use cookies, embed additional third-party tracking, and monitor your interaction with that embedded content, including tracking your interaction with the embedded content if you have an account and are logged in to that website.
## Who we share your data with
If you request a password reset, your IP address will be included in the reset email.
## How long we retain your data
If you leave a comment, the comment and its metadata are retained indefinitely. This is so we can recognise and approve any follow-up comments automatically instead of holding them in a moderation queue.
For users that register on our website (if any), we also store the personal information they provide in their user profile. All users can see, edit, or delete their personal information at any time (except they cannot change their username). Website administrators can also see and edit that information.
## What rights you have over your data
If you have an account on this site, or have left comments, you can request to receive an exported file of the personal data we hold about you, including any data you have provided to us. You can also request that we erase any personal data we hold about you. This does not include any data we are obliged to keep for administrative, legal, or security purposes.
## Where your data is sent
Visitor comments may be checked through an automated spam detection service.
---
### Refund and Returns Policy
Date: 2023-04-28
URL: https://cyfinoid.com/refund_returns/
At Cyfinoid Research, we take great pride in the quality and value of our digital products. We are confident that our customers will be satisfied with their purchases. However, due to the nature of digital goods, our refund policy differs from those of physical products.
Please carefully read our refund policy below before making a purchase:
1. No Refunds: Due to the non-tangible nature of digital products, we cannot offer refunds, exchanges, or returns once a purchase is made. By completing a transaction, you acknowledge and agree to this policy.
2. Exceptions: In the rare event that you encounter a technical issue with your digital product that prevents you from using it as intended, please contact our customer support team at support@cyfinoid.com within 14 days of purchase. Our team will investigate the issue and, if confirmed, provide you with a solution or replacement product of equal or lesser value.
3. Incorrect Purchase: If you accidentally purchase the wrong product, please contact our customer support team immediately at support@cyfinoid.com. We will do our best to assist you, but we cannot guarantee a refund or exchange as per our No Refunds policy.
4. Customer Satisfaction: At Cyfinoid Research, customer satisfaction is our top priority. If you have any concerns, questions, or feedback, please reach out to our customer support team at support@cyfinoid.com. We will do our best to resolve any issues and ensure your satisfaction with our digital products.
By purchasing a digital product from Cyfinoid Research, you confirm that you have read, understood, and accepted our Refund Policy. We encourage you to review this policy periodically, as we reserve the right to modify it at any time without prior notice.
Thank you for your understanding and support.
---
### Break & Fix Web Applications
Date: 2023-01-13
URL: https://cyfinoid.com/trainings/break-fix-web-applications/
**[THIS COURSE IS NOW RETIRED AND IS SUPERSEEDED BY ATTACK AND DEFEND SOFTWARE SUPPLY CHAIN.](https://cyfinoid.com/trainings/attack-defend-software-supply-chain/)**
### How to attend
Cyfinoid offers its trainings via multiple international conference. Details for the next class will be updated here.
[Contact Us for Private / Corporate Session](https://cyfinoid.com/contact/)
---
### Distributed Web
Date: 2023-01-12
URL: https://cyfinoid.com/research/distributed-web/
The distributed web encompasses a wide range of technologies and communities that are working towards creating a more open, transparent, and secure internet where users have more control over their own data and online identity. This includes both blockchain-based solutions, as well as those based on protocols such as ActivityPub and the IndieWeb movement.
One of the key features of the distributed web is that it allows users to take control of their own data and online identity, rather than relying on centralised entities to do so. As the distributed web is still in its early stages of development, we at Cyfinoid Research have chosen to focus on researching these technologies in order to advance the field and create solutions (both offensive and defensive solutions) that can effectively protect against potential threats and empower users. We believe that the decentralised web has the potential to revolutionise various industries such as finance, social media, and gaming, and we are committed to contributing to this rapidly growing field.
## Community Contributions
- Fediverse OSINT
Fediverse
- Fediverse Monitoring
Fediverse, Intern-project
Fediverse OSINT

🌐 Mapping the Fediverse, one handle at a time.
**Fediverse OSINT** is a lightweight tool to collect publicly accessible metadata from Fediverse platforms like Mastodon, Misskey, and more. Whether you’re tracking mentions, discovering linked accounts, or mapping user behavior — this tool helps you gather intelligence with minimal footprint.
### With Fediverse OSINT, you can:
✅ Perform OSINT on **any known handle** across Mastodon, Pleroma, Misskey, etc.**✅ Extract profile metadata (bio, links, tags, followers/following)✅ Analyze public post content for keywords, hashtags, domains, or mentions✅ Identify cross-platform behavior through linked URLs and common identifiers✅ Leverage federation protocols to track visibility and reach✅ Get results in a format that’s human-readable or export-friendly
### Why it works well for open source intelligence:
🔍 Focused on public-facing data only — no scraping or unauthorized access📡 Lightweight Python script with clear CLI usage📦 No dependencies on API tokens (where possible)💡 Great for journalists, researchers, threat intel analysts, and curiosity-driven hackers
Source Code: [https://github.com/cyfinoid/fediverse_osint](https://github.com/cyfinoid/fediverse_osint)
The Fediverse is growing fast. So is the need to understand how public discourse flows across decentralized networks. This tool gives you a head start.
Categories :
Fediverse
Fediverse Monitoring
Internship Project**
**Author: [Vansh Bulani](https://www.linkedin.com/in/vanshbulani/)**
The Fediverse is a collection of interconnected yet independent social networks that can communicate seamlessly using open protocols. Users on one platform can follow, interact with, and receive updates from users on entirely different platforms – all while staying within their preferred service. Most Fediverse platforms are free and open-source, fostering transparency and community-driven development.
Thanks to these open protocols, a wealth of data is publicly accessible through the right APIs. This project leverages that openness to collect and analyze various statistics across the Fediverse, providing deeper insights into its scale, activity, and growth.
**Project Link: [https://github.com/cyfinoid/fediverse-monitoring](https://github.com/cyfinoid/fediverse-monitoring)**
Categories :
Fediverse, Intern-project
## Blogs
####
[Automating a Known Weakness: Introducing keychecker](https://cyfinoid.com/automating-a-known-weakness-introducing-keychecker/)
22nd August 2025
No Comments
[ ](https://cyfinoid.com/automating-a-known-weakness-introducing-keychecker/)
[](https://cyfinoid.com/automating-a-known-weakness-introducing-keychecker/)
####
[Cyfinoid Research at Hacker Summer Camp 2024](https://cyfinoid.com/cyfinoid-research-at-hacker-summer-camp-2024/)
30th July 2024
1 Comment
[ ](https://cyfinoid.com/cyfinoid-research-at-hacker-summer-camp-2024/)
[](https://cyfinoid.com/cyfinoid-research-at-hacker-summer-camp-2024/)
---
### Android
Date: 2023-01-12
URL: https://cyfinoid.com/research/android/
> Android security was one of Cyfinoid’s earlier core research areas. This page remains live as an archive of that work because it led to useful tools, internship projects, training material, and practical lessons that still matter to mobile security practitioners.
Android is no longer one of our primary active research pillars. Our current active focus areas are [Software Supply Chain Security](https://cyfinoid.com/research/software-supply-chain-security/), [Cloud Security](https://cyfinoid.com/research/cloud-security/), and [AI usage and security](https://cyfinoid.com/research/ai-usage-and-security/). Even so, the Android work remains part of our history and continues to reflect the research-driven approach that shaped the company.
## Archived Research Focus
Our Android work looked at security as a full ecosystem problem rather than a narrow reverse-engineering exercise. That included application analysis, device and network considerations, development practices, and the kinds of workflows security engineers use when they need to assess real mobile apps under time pressure.
We were especially interested in making Android security analysis more practical, repeatable, and accessible through hands-on labs, vulnerable targets, and tooling that could help bridge the gap between deep analysis and everyday assessment workflows.
### Community Contributions
- APK Analysis Automation
Android, Intern-project
- CFYVuln-Android
Android, Intern-project
## What This Work Covered
- Static and dynamic analysis of Android applications
- Root detection bypass and instrumentation-driven testing
- Traffic interception and application behavior analysis
- Hybrid mobile application assessment, including React Native and Flutter
- Threat modeling and practical defensive improvements for Android applications
## Why Keep This Page Live
- It documents an important earlier phase of Cyfinoid’s research
- It helps previous students, collaborators, and readers find older work
- It preserves projects and ideas that still have practical value
If you are looking for our current active research priorities, start with Software Supply Chain Security, Cloud Security, and AI usage and security.
### Blogs
####
[SBOMPlay v0.0.7](https://cyfinoid.com/sbomplay-v0-0-7/)
31st December 2025
No Comments
[ ](https://cyfinoid.com/sbomplay-v0-0-7/)
[](https://cyfinoid.com/sbomplay-v0-0-7/)
####
[GH Navigator Released: Full Coverage of GitHub’s Data and Control Planes](https://cyfinoid.com/gh-navigator-released-full-coverage-of-githubs-data-and-control-planes/)
23rd September 2025
No Comments
[ ](https://cyfinoid.com/gh-navigator-released-full-coverage-of-githubs-data-and-control-planes/)
[](https://cyfinoid.com/gh-navigator-released-full-coverage-of-githubs-data-and-control-planes/)
####
[Decouple and Conquer: Understanding Control and Data Planes Across Technology](https://cyfinoid.com/decouple-and-conquer-understanding-control-and-data-planes-across-technology/)
23rd September 2025
No Comments
[ ](https://cyfinoid.com/decouple-and-conquer-understanding-control-and-data-planes-across-technology/)
[](https://cyfinoid.com/decouple-and-conquer-understanding-control-and-data-planes-across-technology/)
####
[Automating a Known Weakness: Introducing keychecker](https://cyfinoid.com/automating-a-known-weakness-introducing-keychecker/)
22nd August 2025
No Comments
[ ](https://cyfinoid.com/automating-a-known-weakness-introducing-keychecker/)
[](https://cyfinoid.com/automating-a-known-weakness-introducing-keychecker/)
####
[Introducing 3P-Tracer: third-party mapping in your browser](https://cyfinoid.com/introducing-3p-tracer-third-party-mapping-in-your-browser/)
29th July 2025
No Comments
[ ](https://cyfinoid.com/introducing-3p-tracer-third-party-mapping-in-your-browser/)
[](https://cyfinoid.com/introducing-3p-tracer-third-party-mapping-in-your-browser/)
####
[Introducing SBOM Play: A Privacy-First SBOM Explorer with Vulnerability & License Insights](https://cyfinoid.com/introducing-sbom-play-a-privacy-first-sbom-explorer-with-vulnerability-license-insights/)
17th July 2025
No Comments
[ ](https://cyfinoid.com/introducing-sbom-play-a-privacy-first-sbom-explorer-with-vulnerability-license-insights/)
[](https://cyfinoid.com/introducing-sbom-play-a-privacy-first-sbom-explorer-with-vulnerability-license-insights/)
1
[2](https://cyfinoid.com/llms-full.txt/page/2/)
[Next »](https://cyfinoid.com/llms-full.txt/page/2/)
### Previous Training Sessions
### [Attack & Defend Android Application BlackHat Asia 2025](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-android-applications-online--43045)
1 April 2025 – 2 April 2025Online[](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-android-applications-online--43045)
### [Attack & Defend Android Applications c0c0n 2024](https://india.c0c0n.org/2024/attack-and-defend-android-applications)
13 November 2024 – 14 November 2024Gandhinagar, Gujrat[](https://india.c0c0n.org/2024/attack-and-defend-android-applications)
### [Attack & Defend Android Applications BlackHat USA 2024](https://www.blackhat.com/us-24/training/schedule/index.html#attack-and-defend-android-applications-virtual-374731705525315)
5 August 2024 – 6 August 2024Virtual[](https://www.blackhat.com/us-24/training/schedule/index.html#attack-and-defend-android-applications-virtual-374731705525315)
### [Attack & Defend Android Applications BlackHat USA 2024](https://www.blackhat.com/us-24/training/schedule/index.html#attack-and-defend-android-applications-virtual-37473)
3 August 2024 – 4 August 2024Virtual[](https://www.blackhat.com/us-24/training/schedule/index.html#attack-and-defend-android-applications-virtual-37473)
### [Attack & Defend Android Applications BlackHat USA 2023](https://www.blackhat.com/us-23/training/schedule/index.html#attack-and-defend-android-applications-30724)
5 August 2023 – 6 August 2023Las Vegas, USA[](https://www.blackhat.com/us-23/training/schedule/index.html#attack-and-defend-android-applications-30724)
### [Attack & Defend Android Applications BlackHat USA 2022](https://www.blackhat.com/us-22/training/schedule/index.html#attack-and-defend-android-applications-256601645123759)
8 August 2022 – 9 August 2022Las Vegas, USA[](https://www.blackhat.com/us-22/training/schedule/index.html#attack-and-defend-android-applications-256601645123759)
### [Attack & Defend Android Applications BlackHat USA 2022](https://www.blackhat.com/us-22/training/schedule/index.html#attack-and-defend-android-applications-25660)
6 August 2022 – 7 August 2022Las Vegas, USA[](https://www.blackhat.com/us-22/training/schedule/index.html#attack-and-defend-android-applications-25660)
Note:
Android is a trademark of Google Inc
---
### About Us
Date: 2023-01-12
URL: https://cyfinoid.com/about/
Cyfinoid Research is a boutique research and training firm that is dedicated to innovative research in the fields of android and decentralized technology. By sharing our findings through our training programs, we aim to educate and inspire others to pursue their own research and make meaningful contributions to these exciting and rapidly-evolving fields. At Cyfinoid Research, we are committed to staying at the forefront of our industry and staying up-to-date on the latest developments in android and decentralized technology. Whether through our research or our training programs, we strive to make a positive impact on the world around us.
Feel free to contact us via the form below for more details
Your name
Your email
Subject
Enquiry Type
Training EnquiryResearch CollaborationPentesting ServicesInternship Opportunities
Your Message (optional)
Δdocument.getElementById( "ak_js_1" ).setAttribute( "value", ( new Date() ).getTime() );
---
### Web Applications
Date: 2023-01-12
URL: https://cyfinoid.com/research/web-application/
At Cyfinoid Research, we understand that web applications play a critical role in our daily interactions with the world and as such, web application security is a major area of focus for us. As cyber threats continue to evolve, it’s crucial to stay ahead of the curve and develop new and innovative ways to protect against them. That’s why we have chosen to focus on three key areas within web application security for now:
**Supply Chain Security**: The software supply chain is a critical component of web application security, as it encompasses all the processes involved in creating, distributing, and maintaining software. Our research in this area focuses on identifying and mitigating risks throughout the software supply chain, such as identifying and addressing vulnerabilities in third-party libraries and components.
**Code-assisted security analysis**: We are developing new and innovative techniques for automatically analyzing and assessing the security of web applications. This includes static and dynamic analysis, as well as using machine learning to identify vulnerabilities and potential attack vectors.
**DevSecOps** : Empowering devops team with security knowledge: We are working to empower devops teams with the knowledge and tools they need to handle security in an efficient and effective manner. This includes developing new security methodologies and best practices for devops teams to follow and providing training on how to integrate security into the development process.

We believe that by focusing on these key areas, we can make a meaningful impact on the field of web application security, and help to create a safer and more secure online environment for everyone.
### Related Blogposts
####
[Enhancing Open Source Security for Startups with Automated Scanning](https://cyfinoid.com/enhancing-open-source-security-for-startups-with-automated-scanning/)
[Read More](https://cyfinoid.com/enhancing-open-source-security-for-startups-with-automated-scanning/)
[ ](https://cyfinoid.com/enhancing-open-source-security-for-startups-with-automated-scanning/)
[](https://cyfinoid.com/enhancing-open-source-security-for-startups-with-automated-scanning/)
### Current Training Offerings
Deprecated shortcode. Use `
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
1 August 2026 - 2 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
### [Attacking Cloud Environments (AWS, Azure, GCP, DigitalOcean and Aliyun) BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-51037)
1 August 2026 - 2 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-51037)
### [Attacking Cloud Environments (AWS, Azure, GCP, DigitalOcean and Aliyun) BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-510371770400827)
3 August 2026 - 4 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-510371770400827)
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
3 August 2026 - 4 August 2026[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
### [Mastering Third-Party Risk Management : Vendor & Software Supply Chain BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
Date: 4 August 2026Las Vegas, USA[](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)` instead.
### Previous Trainings
Deprecated shortcode. Use `
### [0wning the Cloud – AWS, Azure, GCP, DigitalOcean and Aliyun BlackHat EU 2025](https://www.blackhat.com/eu-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-46968)
8 December 2025 - 9 December 2025London, UK[](https://www.blackhat.com/eu-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-46968)
### [Attack and Defend Software Supply Chain DEFCON Trainings 2025](https://training.defcon.org/collections/def-con-training-las-vegas-2025/products/attack-and-defend-software-supply-chain-las-vegas-2025)
11 August 2025 - 12 August 2025Las Vegas, USA[](https://training.defcon.org/collections/def-con-training-las-vegas-2025/products/attack-and-defend-software-supply-chain-las-vegas-2025)
### [0wning the Cloud – AWS, Azure, GCP, DigitalOcean and Aliyun BlackHat USA 2025](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-445131736885703)
4 August 2025 - 5 August 2025Las Vegas, USA[](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-445131736885703)
### [0wning the Cloud – AWS, Azure, GCP, DigitalOcean and Aliyun BlackHat USA 2025](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-44513)
2 August 2025 - 3 August 2025Las Vegas, USA[](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-44513)
### [Attacking CI/CD Environments BruCON Trainings](https://www.brucon.org/training-details/attacking-cicd)
24 April 2025 - 25 April 2025Online[](https://cyfinoid.com/event/pipeline-predators-attacking-ci-cd-environments-brucon-trainings/)
### [Attack & Defend Android Application BlackHat Asia 2025](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-android-applications-online--43045)
1 April 2025 - 2 April 2025Online[](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-android-applications-online--43045)
### [Attack & Defend Software Supply Chain BlackHat Asia 2025](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-software-supply-chain-online--43054)
1 April 2025 - 2 April 2025Online[](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-software-supply-chain-online--43054)
### [Attack & Defend Software Supply Chains Nullcon 2025](https://nullcon.net/goa-2025/training/attack-and-defend-software-supply-chains)
3 March 2025 - 5 March 2025Goa, India[](https://cyfinoid.com/event/attack-defend-software-supply-chains-nullcon-2025/)
### [Attack & Defend Android Applications c0c0n 2024](https://india.c0c0n.org/2024/attack-and-defend-android-applications)
13 November 2024 - 14 November 2024Gandhinagar, Gujrat[](https://india.c0c0n.org/2024/attack-and-defend-android-applications)
### [Attack & Defend Android Applications BlackHat USA 2024](https://www.blackhat.com/us-24/training/schedule/index.html#attack-and-defend-android-applications-virtual-374731705525315)
5 August 2024 - 6 August 2024Virtual[](https://www.blackhat.com/us-24/training/schedule/index.html#attack-and-defend-android-applications-virtual-374731705525315)` instead.
---
### Research Areas
Date: 2023-01-12
URL: https://cyfinoid.com/research/
Cyfinoid Research focuses on security problems where trust, automation, and attacker behavior collide. We study how modern systems are built, connected, and operated, then turn that research into public tooling, writeups, conference talks, and hands-on training.
Our current active research priorities are Software Supply Chain Security, Cloud Security, and AI usage and security. These are the areas where we are actively investing in new tools, public material, and deeper technical exploration.
Android security remains an important part of our history and previous work. We are keeping that material visible as an older research area because it produced useful tools, labs, and ideas, but it is no longer one of our primary active research pillars.
## Active Research Areas
[](https://cyfinoid.com/research/software-supply-chain-security/)
### Software Supply Chain
The trust relationships that shape modern software delivery from developer workstations security, repositories, tokens, CI/CD pipelines, SAST tooling, package ecosystems, artifacts, provenance, deployment systems to cloud environments
[](https://cyfinoid.com/research/cloud-security/)
### Cloud Environments
How attackers discover, chain, and abuse trust boundaries in cloud environments across identities, storage, metadata, orchestration, automation, and service-to-service relationships.
[](https://cyfinoid.com/research/ai-usage-and-security/)
### AI: Usage & Security
How AI systems are being adopted in real workflows and where that adoption creates new security, privacy, governance, and trust problems.
## Earlier Research Area
### [Android](https://cyfinoid.com/research/android/)
Android security was one of Cyfinoid’s earlier focus areas. That work led to hands-on research, internship projects, training material, and tools that remain useful to mobile security practitioners.
While Android is no longer one of our main active research priorities, we are keeping the material available as an archive of previous work and a record of what shaped our current approach to research-driven training.
## How Research Shows Up
- Public tools and experiments
- Blog posts, writeups, and practical notes
- Conference talks, workshops, and training material
- Research-informed consulting and private engagements
## Research Philosophy
We prefer work that is practical, testable, and useful outside a slide deck. That often means building tools, creating reproducible labs, publishing explainers, and focusing on problems that sit at the intersection of offensive understanding and defensive decision-making.
If you want to collaborate, invite us to speak, or discuss research-led training or consulting, [contact us](https://cyfinoid.com/contact/).
---
### Trainings
Date: 2023-01-12
URL: https://cyfinoid.com/trainings/
Cyfinoid trainings are built from ongoing research, real-world offensive experience, and the technical problems modern teams actually struggle with in software delivery and cloud environments. We focus on practical material that helps participants understand how systems are attacked in practice, how trust breaks across connected platforms, and how better defensive decisions can be made as a result.
Our current training lineup is strongest in Cloud Security and Software Supply Chain Security, including the CI/CD environments that connect source code, automation, artifacts, and deployment. These are the areas where our research, tooling, and hands-on labs most directly feed into the classroom.
We deliver trainings at major security conferences and through private / corporate sessions. Exact syllabi vary by event, audience, duration, and lab design, so each course page gives the high-level approach while the specific conference page remains authoritative for the exact modules, student requirements, and logistics for that run.
## Current Training Programs
### [Hacking Multi-Cloud Infrastructure](https://cyfinoid.com/trainings/hacking-multi-cloud-infrastructure/)
This training helps participants think about cloud environments the way attackers do. Instead of memorizing one provider at a time, the focus is on trust boundaries, identity, storage, metadata, orchestration, automation, and the patterns that repeat across cloud ecosystems.
It is designed for teams that want an attacker-informed view of cloud risk across AWS, Azure, GCP, DigitalOcean, Alibaba Cloud, Kubernetes platforms, and adjacent cloud-native environments, depending on the run.
### [Attack & Defend Software Supply Chain](https://cyfinoid.com/trainings/attack-defend-software-supply-chain/)
This training looks at software trust across the full delivery lifecycle, not just dependencies and SBOMs. It covers the producer writing first-party code, the consumer building on top of third-party software and services, and the end user depending on the final product.
The material spans the developer desktop, repositories, CI/CD, package ecosystems, artifacts, deployment tooling, and cloud environments. Public conference runs are typically attack-led, while private deliveries can go deeper into defense, governance, and operational hardening.
### [Attacking CI/CD Environments](https://cyfinoid.com/trainings/attacking-ci-cd-environments/)
This training focuses on CI/CD as a high-trust control plane rather than simple build automation. Participants learn how attackers abuse repositories, workflows, runners, tokens, artifacts, and integrations, and how those weaknesses can turn into software tampering, secret theft, cloud abuse, or wider supply chain compromise.
It is especially useful for platform teams, DevOps engineers, product security teams, and testers who want a more realistic understanding of how modern delivery pipelines fail under attacker pressure.
## Archived Training
### [Attack & Defend Android Applications](https://cyfinoid.com/trainings/attack-defend-android-applications/)
This course remains part of Cyfinoid’s training history and is kept online as an archive for previous attendees, conference visitors, and people researching our earlier mobile security work. It is no longer offered as a current public or private training.
## Why These Trainings Stand Out
- Research-driven rather than slide-driven
- Built around hands-on labs and realistic attack paths
- Offensive understanding with practical defensive relevance
- Focused on trust boundaries, automation, and how real systems connect
- Flexible enough for conference formats and private team needs
## How To Choose
- Choose Hacking Multi-Cloud Infrastructure if your focus is attacker-informed cloud security across providers and platforms
- Choose Attack & Defend Software Supply Chain if your focus is software trust across the full path from development to deployment
- Choose Attacking CI/CD Environments if your focus is pipeline abuse, automation risk, and software delivery control planes
## How To Attend
Cyfinoid offers these trainings through international conferences and private engagements. For public runs, see the listing below and conference page for the exact syllabus and logistics. For private / corporate sessions, [contact us](https://cyfinoid.com/contact/).
## Upcoming Trainings
### [Attacking Cloud Environments (AWS, Azure, GCP, DigitalOcean and Aliyun) BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-51037)
1 August 2026 – 2 August 2026
[*](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-51037)
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
1 August 2026 – 2 August 2026
[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-51031)
### [Attacking Cloud Environments (AWS, Azure, GCP, DigitalOcean and Aliyun) BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-510371770400827)
3 August 2026 – 4 August 2026
[](https://blackhat.com/us-26/training/schedule/index.html#attacking-cloud-environments-aws-azure-gcp-digitalocean-and-aliyun-510371770400827)
### [Attacking the Software Supply Chain from Dev to Prod BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
3 August 2026 – 4 August 2026
[](https://blackhat.com/us-26/training/schedule/index.html#attacking-the-software-supply-chain-from-dev-to-prod-510311770323829)
### [Mastering Third-Party Risk Management : Vendor & Software Supply Chain BlackHat USA 2026](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
Date: 4 August 2026
Las Vegas, USA
[](https://blackhat.com/us-26/training/schedule/index.html#mastering-third-party-risk-management--vendor--software-supply-chain-51044)
## Testimonials
*
Impressive Content
Great delivery, very attentive, excellent knowledge base provided. The provision of material is a highlight.
**Attendee @ BlackHat USA**
**********
**
Insightful and Well-Worth the Investment
The presenters conveyed a significant amount of knowledge and I’m walking away with good value for $. Excellent work and great training!
**Attendee @ Blackhat USA**
**********
**
Deep dive training
"One of the most detailed training, it dives deep in the cloud hacking and explores real world attacks with case studies & thanks for the self-host vulnerable infra!"
**Attendee @ BlackHat USA**
**********
**
Knowledgeable Trainer and Practical Examples
Great knowledge and very helpful trainer and easy examples to relate with real world problems
**Attendee @ Nullcon**
**********
**
Well-Executed Sessions with a Desire for More
The training was really good and trainers executed it in a fantastic way and they where very helpful. I really like to continue for 2 more days as the contents were interesting but time frame allocated was only 2 days.
**Attendee @ c0c0n**
**********
**
Enjoyable and Insightful Two-Day Workshop
Training Content, Discussions was on point. Really enjoyed two days session.
**Attendee @ c0c0n**
**********
**
Hands-On Learning with Practical Cloud Insights
Learns a lot about Cloud structure and how we can get the leaking information and also how to use it. Well prepared tools and lab environment make us doing well. Really appreciate it.
**Attendee @ BlackHat**
**********
**
Valuable Insights for Real-World Mobile Pentesting
It was a very complete course providing me with very useful information that I will put in practice as I'm part of Mobile Pentest team in my organization, I'm very satisfied with the content and kudos to both instructors, they are pretty amazing with plenty of verifiable experience
**Attendee @ BlackHat USA**
**********
**
Smooth Learning Curve for Newcomers
*I'm a beginner level but was easy for me to understand all the topics because it was very clear the examples for each topic. Thanks for the help.*
**Attendee @ BlackHat USA**
**********
**
This wasn’t your typical cloud security class
This wasn’t your typical cloud security class - it was two full days of hands-on labs, real-world attack scenarios, and deep technical walkthroughs across AWS, Azure, GCP, DigitalOcean, and Aliyun. Each lab pushed us to think like attackers and defenders, and I walked away with a whole new appreciation for how exposed cloud environments can be if not properly secured.
…
[ This wasn’t your typical cloud security classRead More »](https://cyfinoid.com/testimonial/this-wasnt-your-typical-cloud-security-class/)
**Darren Windham**
Principal - Forensic Services / Charles River Associates
**********
## Past Trainings
### [0wning the Cloud – AWS, Azure, GCP, DigitalOcean and Aliyun BlackHat EU 2025](https://www.blackhat.com/eu-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-46968)
8 December 2025 – 9 December 2025
London, UK
[](https://www.blackhat.com/eu-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-46968)
### [Attack and Defend Software Supply Chain DEFCON Trainings 2025](https://training.defcon.org/collections/def-con-training-las-vegas-2025/products/attack-and-defend-software-supply-chain-las-vegas-2025)
11 August 2025 – 12 August 2025
Las Vegas, USA
[](https://training.defcon.org/collections/def-con-training-las-vegas-2025/products/attack-and-defend-software-supply-chain-las-vegas-2025)
### [0wning the Cloud – AWS, Azure, GCP, DigitalOcean and Aliyun BlackHat USA 2025](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-445131736885703)
4 August 2025 – 5 August 2025
Las Vegas, USA
[](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-445131736885703)
### [0wning the Cloud – AWS, Azure, GCP, DigitalOcean and Aliyun BlackHat USA 2025](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-44513)
2 August 2025 – 3 August 2025
Las Vegas, USA
[](https://www.blackhat.com/us-25/training/schedule/index.html#0wning-the-cloud---aws-azure-gcp-digitalocean-and-aliyun-44513)
### [Attacking CI/CD Environments BruCON Trainings](https://www.brucon.org/training-details/attacking-cicd)
24 April 2025 – 25 April 2025
Online
[](https://cyfinoid.com/event/pipeline-predators-attacking-ci-cd-environments-brucon-trainings/)
### [Attack & Defend Software Supply Chain BlackHat Asia 2025](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-software-supply-chain-online--43054)
1 April 2025 – 2 April 2025
Online
[](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-software-supply-chain-online--43054)
### [Attack & Defend Android Application BlackHat Asia 2025](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-android-applications-online--43045)
1 April 2025 – 2 April 2025
Online
[](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-android-applications-online--43045)
### [Attack & Defend Software Supply Chains Nullcon 2025](https://nullcon.net/goa-2025/training/attack-and-defend-software-supply-chains)
3 March 2025 – 5 March 2025
Goa, India
[](https://cyfinoid.com/event/attack-defend-software-supply-chains-nullcon-2025/)
### [Attack & Defend Android Applications c0c0n 2024](https://india.c0c0n.org/2024/attack-and-defend-android-applications)
13 November 2024 – 14 November 2024
Gandhinagar, Gujrat
[](https://india.c0c0n.org/2024/attack-and-defend-android-applications)
### [Attack & Defend Android Applications BlackHat USA 2024](https://www.blackhat.com/us-24/training/schedule/index.html#attack-and-defend-android-applications-virtual-374731705525315)
5 August 2024 – 6 August 2024
Virtual
[](https://www.blackhat.com/us-24/training/schedule/index.html#attack-and-defend-android-applications-virtual-374731705525315)
### [Going beyond shells! – hacking aws, google cloud, digitalocean and aliyun BlackHat USA 2024](https://www.blackhat.com/us-24/training/schedule/index.html#going-beyond-shells---hacking-aws-google-cloud-digitalocean-and-aliyun-virtual-374681706229570)
5 August 2024 – 6 August 2024
Virtual
[](https://www.blackhat.com/us-24/training/schedule/index.html#going-beyond-shells---hacking-aws-google-cloud-digitalocean-and-aliyun-virtual-374681706229570)
### [Attack & Defend Android Applications BlackHat USA 2024](https://www.blackhat.com/us-24/training/schedule/index.html#attack-and-defend-android-applications-virtual-37473)
3 August 2024 – 4 August 2024
Virtual
[](https://www.blackhat.com/us-24/training/schedule/index.html#attack-and-defend-android-applications-virtual-37473)
### [Going beyond shells! – hacking aws, google cloud, digitalocean and aliyun BlackHat USA 2024](https://www.blackhat.com/us-24/training/schedule/index.html#going-beyond-shells---hacking-aws-google-cloud-digitalocean-and-aliyun-virtual-37468)
3 August 2024 – 4 August 2024
Virtual
[](https://www.blackhat.com/us-24/training/schedule/index.html#going-beyond-shells---hacking-aws-google-cloud-digitalocean-and-aliyun-virtual-37468)
### [Attacking CI CD Environments Nullcon Hyderabad 24](https://nullcon.net/hyderabad-2024/training/attacking-ci-cd-environments)
2 May 2024 – 4 May 2024
Hyderabad, India
[](https://nullcon.net/hyderabad-2024/training/attacking-ci-cd-environments)
### [Attack & Defend Software Supply Chain BlackHat Asia](https://www.blackhat.com/asia-24/training/schedule/index.html#attack-and-defend-software-supply-chain-virtual-36009)
16 April 2024 – 17 April 2024
Online
[](https://www.blackhat.com/asia-24/training/schedule/index.html#attack-and-defend-software-supply-chain-virtual-36009)
### [Beyond the Code : Securing your software supply chain c0c0n 2023](https://india.c0c0n.org/2023/beyond-the-code-securing-your-software-supply-chain)
4 October 2023 – 5 October 2023
Kochi, India
[](https://india.c0c0n.org/2023/beyond-the-code-securing-your-software-supply-chain)
### [Attack & Defend Android Applications BlackHat USA 2023](https://www.blackhat.com/us-23/training/schedule/index.html#attack-and-defend-android-applications-30724)
5 August 2023 – 6 August 2023
Las Vegas, USA
[](https://www.blackhat.com/us-23/training/schedule/index.html#attack-and-defend-android-applications-30724)
### [Attack & Defend Android Applications BlackHat USA 2022](https://www.blackhat.com/us-22/training/schedule/index.html#attack-and-defend-android-applications-256601645123759)
8 August 2022 – 9 August 2022
Las Vegas, USA
[](https://www.blackhat.com/us-22/training/schedule/index.html#attack-and-defend-android-applications-256601645123759)
### [Attack & Defend Android Applications BlackHat USA 2022](https://www.blackhat.com/us-22/training/schedule/index.html#attack-and-defend-android-applications-25660)
6 August 2022 – 7 August 2022
Las Vegas, USA
[](https://www.blackhat.com/us-22/training/schedule/index.html#attack-and-defend-android-applications-25660)
---
### Contact Us
Date: 2023-01-12
URL: https://cyfinoid.com/contact/
Contact us using the form below for all your queries. We will try to respond back as soon as humanly possible.
Your name
Your email
Subject
Enquiry Type
Training EnquiryResearch CollaborationPentesting ServicesInternship Opportunities
Your Message (optional)
Δdocument.getElementById( "ak_js_2" ).setAttribute( "value", ( new Date() ).getTime() );
A – 704, Sagar Landmark,
Bhopal, Madhya Pradesh, India – 462041
info@cyfinoid.com
+91-9880166033
---
### Attack & Defend Android Applications
Date: 2022-07-10
URL: https://cyfinoid.com/trainings/attack-defend-android-applications/
> This training is deprecated. Cyfinoid is keeping this page online as an archive so previous attendees, conference visitors, and people researching the class can still find it, but we do not currently offer new public or private deliveries of this course.
Attack & Defend Android Applications was a hands-on training focused on both attacking and defending the Android application ecosystem. It was designed for people who needed a practical, methodical way to assess Android apps across common attack paths, implementation weaknesses, and defensive controls.
The course combined offensive and defensive perspectives rather than treating Android application security as a narrow reverse-engineering exercise. It covered how Android apps are attacked in practice, how security engineers and pentesters can assess them systematically, and how development teams can strengthen their applications and supporting pipelines.
## Training Status
- Deprecated / archived course
- No future public sessions are planned
- Not currently available as a private / corporate workshop
- This page is retained for reference, discoverability, and past attendee context
## Archived Overview
This training covered the Android application ecosystem across both attack and defense. The goal was not to turn beginners into instant experts, but to give participants a repeatable assessment methodology they could apply to real Android applications.
Participants worked through common Android testing and security engineering tasks such as:
- Traffic interception across HTTP, HTTPS, WebSocket, and related protocols
- Root detection bypass
- Static and dynamic analysis
- Dynamic instrumentation with tools such as Frida and Magisk
- Assessment of non-Java / Kotlin mobile apps such as React Native and Flutter
The defensive side of the course focused on helping teams improve Android application security through:
- Application threat modeling
- Identification of security weaknesses
- Adding security into CI / CD pipelines
- Reviewing and prioritizing security findings
- Improving visibility into third-party components and supply chain risks
## Archived Syllabus
### Basics
- Understanding Android OS architecture
- Android permission model
- Inter-process communication
- Intents, binders, and deep linking
- Application structure
### Attack
- Attack surface mapping
- MITRE ATT&CK and OWASP MSTG
- Traffic interception
- Root detection bypass
- Deobfuscating application code
- Dynamic instrumentation
- Static and dynamic analysis
- Hybrid app assessment including React Native, Flutter, and .NET-based apps
### Defend
- Threat modeling
- OWASP MASVS
- Defense strategies
- CI / CD pipeline security for applications
- Static analysis with Semgrep
- Dynamic analysis
- Third-party library tracking
- Supply chain security considerations
## Who This Training Was For
- Application security engineers
- Penetration testers
- Mobile security practitioners
- Engineering teams responsible for Android application security
## Student Requirements
- Basic familiarity with software development and application security concepts
- Comfort with hands-on testing workflows
- Prior Android security experience was helpful, but the course was intended to be methodical rather than assumption-heavy
## What Students Received
- Access to the learning portal and cloud lab environments
- Slide deck for the material covered during the class
- Detailed answer sheets and supporting material for continued practice
## Recent Previous Run
### [Attack & Defend Android Application BlackHat Asia 2025](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-android-applications-online--43045)
1 April 2025 – 2 April 2025
Online
[*](https://www.blackhat.com/asia-25/training/schedule/index.html#attack-and-defend-android-applications-online--43045)
### [Attack & Defend Android Applications c0c0n 2024](https://india.c0c0n.org/2024/attack-and-defend-android-applications)
13 November 2024 – 14 November 2024
Gandhinagar, Gujrat
[](https://india.c0c0n.org/2024/attack-and-defend-android-applications)
### [Attack & Defend Android Applications BlackHat USA 2024](https://www.blackhat.com/us-24/training/schedule/index.html#attack-and-defend-android-applications-virtual-374731705525315)
5 August 2024 – 6 August 2024
Virtual
[](https://www.blackhat.com/us-24/training/schedule/index.html#attack-and-defend-android-applications-virtual-374731705525315)
## Testimonials
*
Impressive Content
Great delivery, very attentive, excellent knowledge base provided. The provision of material is a highlight.
**Attendee @ BlackHat USA**
**********
**
Insightful and Well-Worth the Investment
The presenters conveyed a significant amount of knowledge and I’m walking away with good value for $. Excellent work and great training!
**Attendee @ Blackhat USA**
**********
**
Valuable Insights for Real-World Mobile Pentesting
It was a very complete course providing me with very useful information that I will put in practice as I'm part of Mobile Pentest team in my organization, I'm very satisfied with the content and kudos to both instructors, they are pretty amazing with plenty of verifiable experience
**Attendee @ BlackHat USA**
**********
**
Smooth Learning Curve for Newcomers
*I'm a beginner level but was easy for me to understand all the topics because it was very clear the examples for each topic. Thanks for the help.*
**Attendee @ BlackHat USA**
**********
## Looking For Current Trainings
Cyfinoid no longer offers this Android training. If you are looking for currently active trainings or related private engagements, please visit the current Cyfinoid trainings pages or [contact us](https://cyfinoid.com/contact/).
[Contact Us for Private / Corporate Session](https://cyfinoid.com/contact/)
---
### Blog
Date: 2022-07-10
URL: https://cyfinoid.com/blog/
---