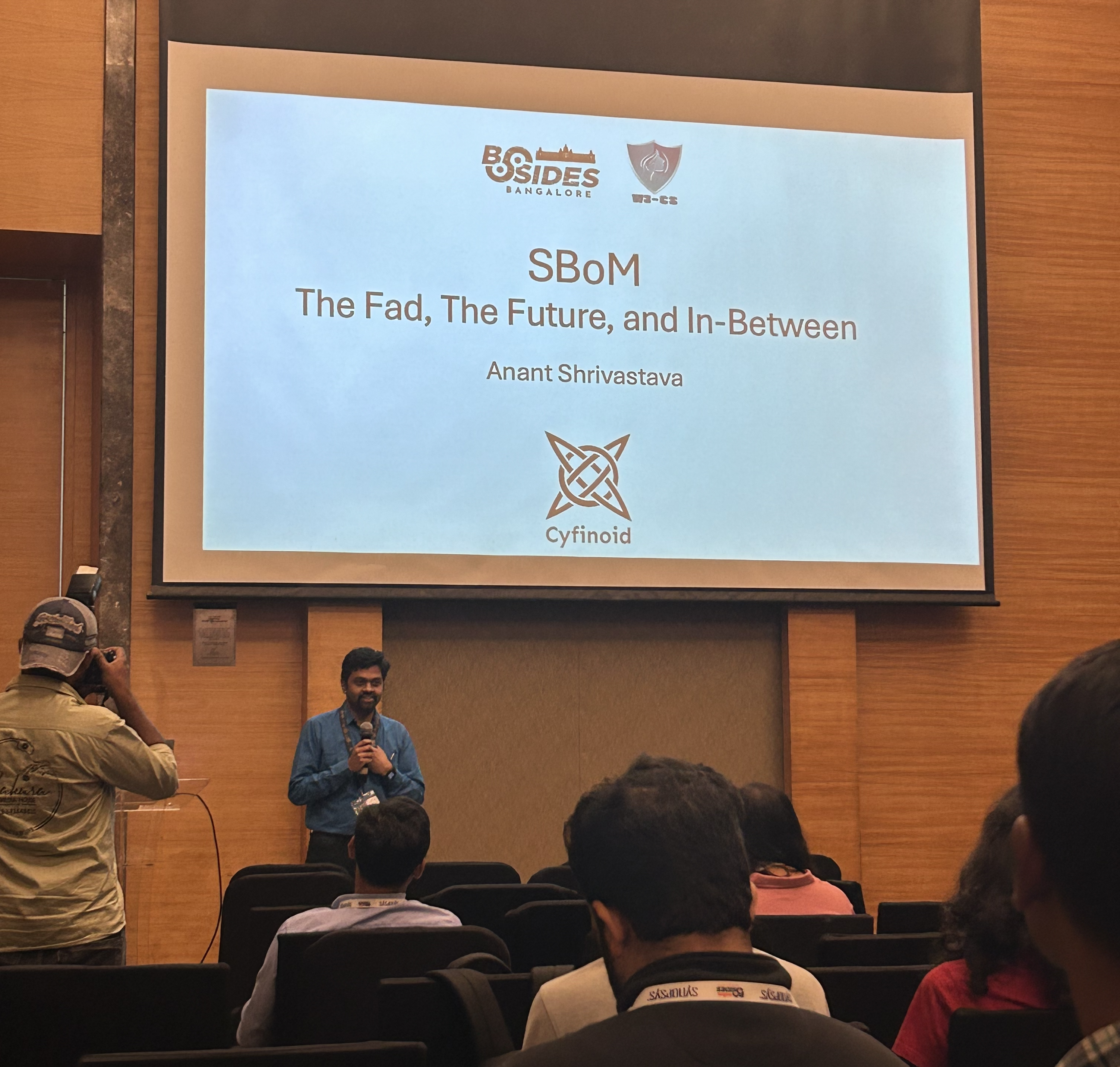
Cybersecurity Research & Training Company
Cyfinoid Research conducts cutting-edge cybersecurity research and turns our findings into hands-on training. Our mission is to spark curiosity, share knowledge, and help others make meaningful contributions to the field.
Research Featured At BlackHat, DEFCON, Nullcon, c0c0n, and other major conferences.





Trusted by 1000+ companies for Security Training & Research.
From startups to Fortune 500s.
Security Research Areas
Focused, original, and deeply technical — our research is designed to challenge assumptions and push boundaries.
Security Trainings
Our trainings are driven by ongoing research. As our findings evolve, so do the curriculum — ensuring fresh, relevant, and practical content.
Upcoming Trainings
Trusted by our
customers & partners












Hacking Multi-Cloud Infrastructure
Cloud providers may use different names, dashboards, and defaults, but attackers keep finding the same weak assumptions underneath. Hacking Multi-Cloud Infrastructure is designed to help participants think about the cloud the way attackers do: through identity, storage, metadata, orchestration, automation, trust boundaries, and the control-plane decisions that quietly shape real risk.
Instead of teaching a checklist for a single vendor, the training focuses on the patterns that transfer across environments. Participants learn how exposed assets are discovered, how identity assumptions get abused, how workloads and services can be pivoted through, and how cloud-native features such as Kubernetes, serverless, and automation expand the attack surface in ways many teams underestimate.
Depending on the delivery, the material may draw from AWS, Azure, Google Cloud, DigitalOcean, Alibaba Cloud, Kubernetes platforms, and adjacent cloud-native ecosystems. The exact service coverage changes from run to run, but the attacker methodology remains the core value: understanding which cloud attack paths are provider-specific, which ones repeat across providers, and how to adapt quickly instead of memorizing screens.
Key topics include:
- Enumerating cloud assets (S3 buckets, IAM roles, Spaces, OSS) without credentials
- Abusing SSRF and IMDSv2 for privilege escalation
- IAM exploitation on AWS, GCP, and Alibaba Cloud
- Escaping GKE clusters and impersonating service accounts on Google Cloud
- Attacking DigitalOcean Spaces and ECS instances
- Exploiting triggers and misconfigurations in AWS Lambda and lesser-known services
- Multi-cloud pivoting and lateral movement using native APIs
- Real-world breach simulations and pentest-inspired cloud lab scenarios
Students will gain repeatable methodologies, guided labs, and post-training resources to practice cloud offensive techniques in a safe environment.
This makes the training especially valuable for red teamers, pentesters, cloud security engineers, incident responders, and platform teams that want an attacker-informed view of cloud risk. It is built for people who want sharper thinking, practical attack-path understanding, and cloud security lessons they can carry from one environment to another.
Attack & Defend Software Supply Chain
Software supply chain security is bigger than SBOMs, dependency lists, and compliance checkboxes. Attack & Defend Software Supply Chain is built around the full trust path that modern software depends on: the developer desktop, source repositories, CI/CD pipelines, package ecosystems, artifacts, deployment systems, containers, and the cloud environments where software finally runs.
The training also reflects the fact that software supply chain risk looks different depending on who you are. A producer writing first-party code has one set of responsibilities. A consumer taking libraries, platforms, and external services into a product has another. An end user deploying or relying on the finished software faces a different trust problem again. This course helps participants understand those perspectives together rather than treating supply chain security as a dependency-only problem.
Public conference deliveries are typically attack-led and focus heavily on how supply chain compromise happens in practice: malicious dependencies, repository abuse, CI/CD attacks, artifact trust failures, cloud-linked pivots, and the weak assumptions attackers exploit. Private and corporate deliveries can go deeper into defense, governance, hardening, provenance, and practical measures teams can use to reduce risk across their own software delivery lifecycle.
The result is a 360-degree view of software trust from code creation to cloud deployment. This training is ideal for developers, platform teams, DevOps practitioners, application security teams, and leaders who want to understand not just where supply chain risk exists, but how it actually turns into compromise and what a stronger defense model looks like in practice.
Key topics include:
- Attacking VS Code, IDE/browser extensions, Git misconfigurations, CI/CD, and package ecosystems
- Creating malicious dependencies and exploiting deployment systems (e.g., GitHub Actions, ArgoCD)
- Cloud & Kubernetes attack paths: IAM abuse, misconfigured images, insecure defaults
- Defense strategies based on SLSA, NIST SSDF, and governance-first models
- Generating and managing SBOMs, securing provenance, cloud audits, and runtime protection
- Role-based responsibilities, breach response, and infrastructure setup for red/blue team practice
Each module includes hands-on labs, real-world attack simulations, and post-training resources to continue your learning journey.
Attacking CI/CD Pipelines
CI/CD systems are no longer just build automation. They are high-trust control planes that connect source code, secrets, runners, artifacts, cloud permissions, and deployment paths. Attacking CI/CD Environments is built around that reality, showing participants how attackers see pipelines not as internal plumbing, but as some of the most valuable infrastructure in the modern software delivery stack.
The training focuses on how real attack paths emerge across repositories, workflow triggers, runners, agents, tokens, logs, caches, artifacts, webhooks, and external integrations. Participants learn how insecure defaults, workflow design mistakes, over-permissioned automation, and poorly isolated runners can create leverage for code tampering, secret theft, persistence, cloud abuse, and broader supply chain compromise.
Rather than centering on one platform alone, the course explores patterns that appear across GitHub Actions, GitLab CI, Jenkins, Bitbucket Pipelines, self-hosted runner environments, and related delivery workflows. It is attack-led by design, but it also helps participants think more clearly about misconfiguration audits, defensive review priorities, and the hardening decisions that matter most when pipelines are treated as critical trust infrastructure.
This makes the training especially relevant for DevOps engineers, build and platform teams, product security teams, application security professionals, and testers who need a realistic understanding of how modern delivery systems fail under attacker pressure. For organizations building and shipping software at speed, this course helps close the gap between “pipeline works” and “pipeline can actually be trusted.”
Key topics include:
- CI/CD fundamentals, architecture, and role in SDLC
- Common attack vectors and real-world CI/CD breaches
- Platform-specific attacks:
- GitHub: Context injection, workflow tampering, secrets leakage, and malicious actions
- Jenkins: Script console abuse, plugin exploits, build artifact tampering
- GitLab CI: Runner exploitation, pipeline manipulation, insecure defaults
- Cloud-native CI/CD misconfigurations and IAM flaws
- Using CI/CD systems for persistence, stealth, and C2
Students gain hands-on experience through labs and a live CTF to reinforce exploitation techniques in realistic enterprise setups.
TESTIMONIALS
What Students Say About Us